
Microsoft has patched today a Windows Defender SmartScreen zero-day exploited in the wild by a financially motivated threat group to deploy the DarkMe remote access trojan (RAT).
The hacking group (tracked as Water Hydra and DarkCasino) was spotted using the zero-day (CVE-2024-21412) in attacks on New Year's Eve day by Trend Micro security researchers.
"An unauthenticated attacker could send the targeted user a specially crafted file that is designed to bypass displayed security checks," Microsoft said in a security advisory issued today.
"However, the attacker would have no way to force a user to view the attacker-controlled content. Instead, the attacker would have to convince them to take action by clicking on the file link."
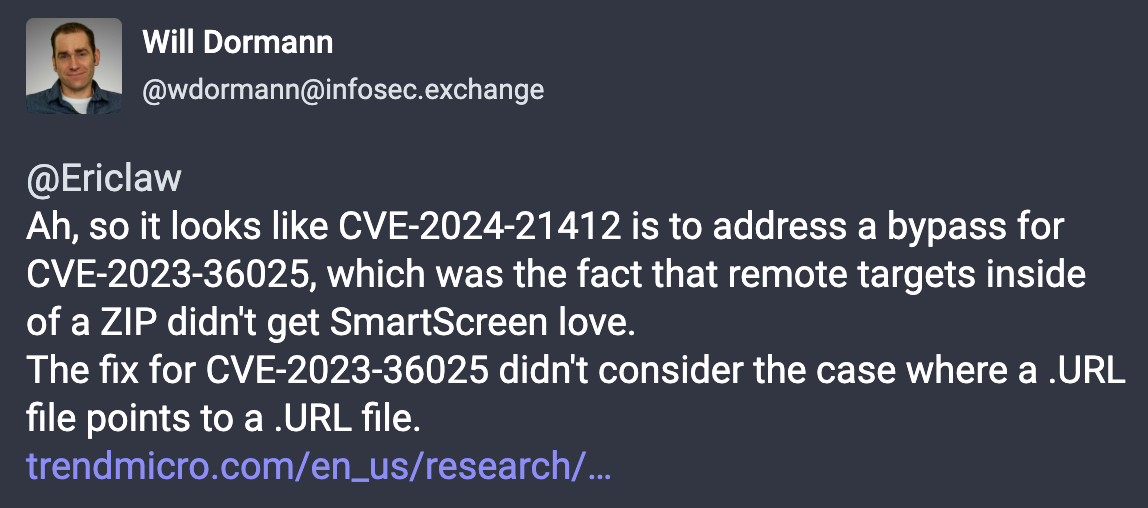
Trend Micro security researcher Peter Girnus, credited for reporting this zero-day, revealed that the CVE-2024-21412 flaw bypasses another Defender SmartScreen vulnerability (CVE-2023-36025).
CVE-2023-36025 was patched during the November 2023 Patch Tuesday, and, as Trend Micro revealed last month, it was also exploited to bypass Windows security prompts when opening URL files to deploy the Phemedrone info-stealer malware.
Zero-day used to target financial market traders
The zero-day that Microsoft patched today was used in attacks targeting "foreign exchange traders participating in the high-stakes currency trading market," with the likely end goal being data theft or ransomware deployment at a later stage.
"In late December 2023, we began tracking a campaign by the Water Hydra group that contained similar tools, tactics, and procedures (TTPs) that involved abusing internet shortcuts (.URL) and Web-based Distributed Authoring and Versioning (WebDAV) components," Trend Micro explained.
"We concluded that calling a shortcut within another shortcut was sufficient to evade SmartScreen, which failed to properly apply Mark-of-the-Web (MotW), a critical Windows component that alerts users when opening or running files from an untrusted source."
Water Hydra exploited CVE-2024-21412 to target forex trading forums and stock trading Telegram channels in spearphishing attacks, pushing a malicious stock chart linking to a compromised trading information site from Russia (fxbulls[.]ru) impersonating a forex broker platform (fxbulls[.]com).
The attackers' goal was to trick targeted traders into installing the DarkMe malware via social engineering.
Tactics they used include posting messages in English and Russian asking for or offering trading guidance and disseminating counterfeit stock and financial tools related to graph technical analysis and graph indicator tools.
A complete list of indicators of compromise (IoCs) for this newly observed DarkMe malware campaign is available here.
The Water Hydra hackers have exploited other zero-day vulnerabilities in the past. For instance, they used a high-severity vulnerability (CVE-2023-38831) in the WinRAR software used by over 500 million users to compromise trading accounts several months before a patch was available.
Other vendors later linked CVE-2023-38831 exploitation to multiple government-backed hacking groups, including the Sandworm, APT28, APT40, DarkPink (NSFOCUS), and Konni (Knownsec) threat groups from Russia, China, and North Korea.
Today, Microsoft patched a second Windows SmartScreen zero-day (CVE-2024-21351) exploited in the wild that could let attackers inject code into SmartScreen and gain code execution.


Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now