
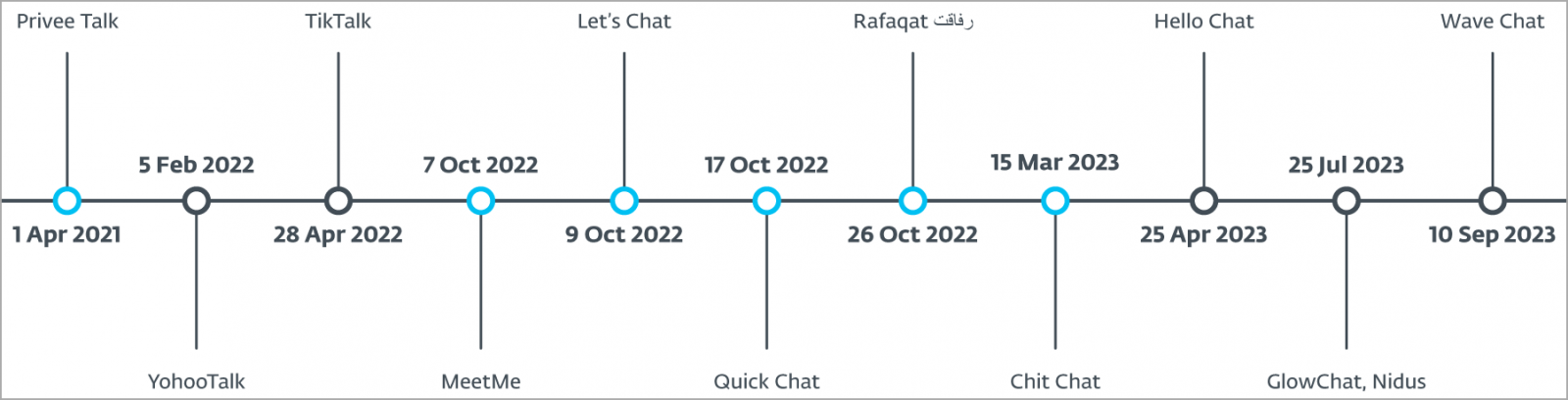
An Android remote access trojan (RAT) known as VajraSpy was found in 12 malicious applications, six of which were available on Google Play from April 1, 2021, through September 10, 2023.
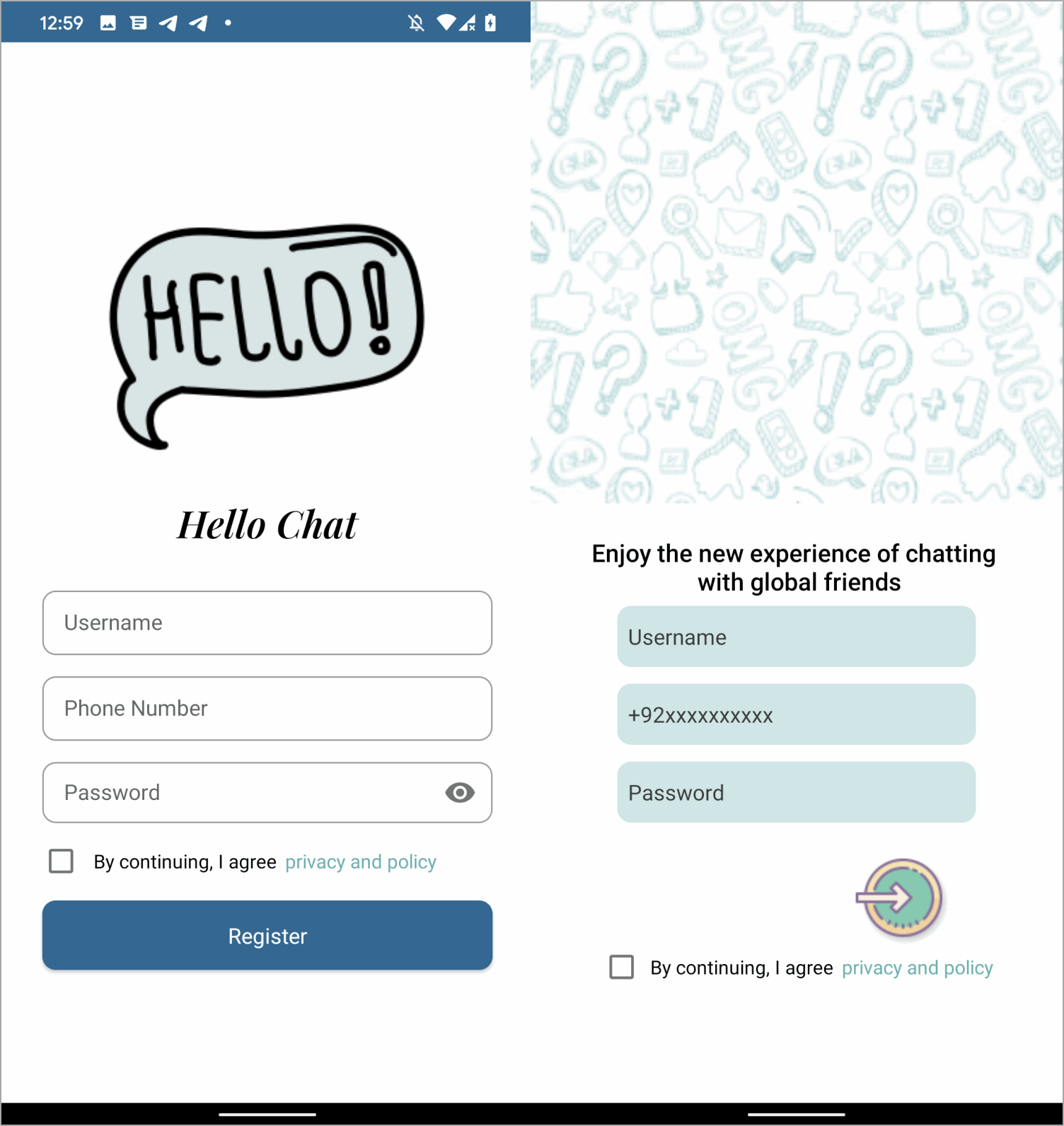
The malicious apps, which have now been removed from Google Play but remain available on third-party app stores, are disguised as messaging or news apps.
Those installing the apps became infected with VajraSpy, allowing the malware to steal personal data, including contacts and messages, and depending on the granted permissions, even to record their phone calls.
ESET researchers who uncovered the campaign report that its operators are the Patchwork APT group, which has been active since at least late 2015, primarily targeting users in Pakistan.
In 2022, the threat actor unintentionally revealed details of their own campaign when they accidentally infected their infrastructure with the 'Ragnatela' RAT, a tool they were employing at the time. This misstep provided Malwarebytes with a window into the Patchwork's operations.
The link between VajraSpy and the activity cluster that ESET identifies as Patchwork was first established by QiAnXin in 2022 (attributing to APT-Q-43), followed by Meta in March 2023, and Qihoo 360 in November 2023 (attributing to APT-C-52).
Android espionage
ESET researcher Lukas Stefanko found 12 malicious Android applications containing the same VajraSpy RAT code, six of which were uploaded on Google Play, where they were downloaded roughly 1,400 times.
The apps that were available on Google Play are:
- Rafaqat رفاقت (news)
- Privee Talk (messaging)
- MeetMe (messaging)
- Let's Chat (messaging)
- Quick Chat (messaging)
- Chit Chat (messaging)
VajraSpy apps available outside Google Play are all bogus messaging apps:
- Hello Chat
- YohooTalk
- TikTalk
- Nidus
- GlowChat
- Wave Chat
Third-party app stores do not report download counts, so the number of people who have installed them through these platforms is unknown.
ESET's telemetry analysis indicates that most victims are located in Pakistan and India and are most likely tricked into installing the fake messaging apps via a romance scam.
VajraSpy is a spyware and RAT that supports various espionage functionalities that mostly revolve around data theft. Its capabilities are summarized as follows:
- Gather and transmit personal data from the infected device, including contacts, call logs, and SMS messages.
- Intercept and extract messages from popular encrypted communication apps like WhatsApp and Signal.
- Record phone calls to enable eavesdropping of private conversations.
- Active the device's camera to take pictures, turning it into a surveillance tool.
- Intercept notifications from various apps in real time.
- Search and exfiltrate documents, images, audio, and other types of files.
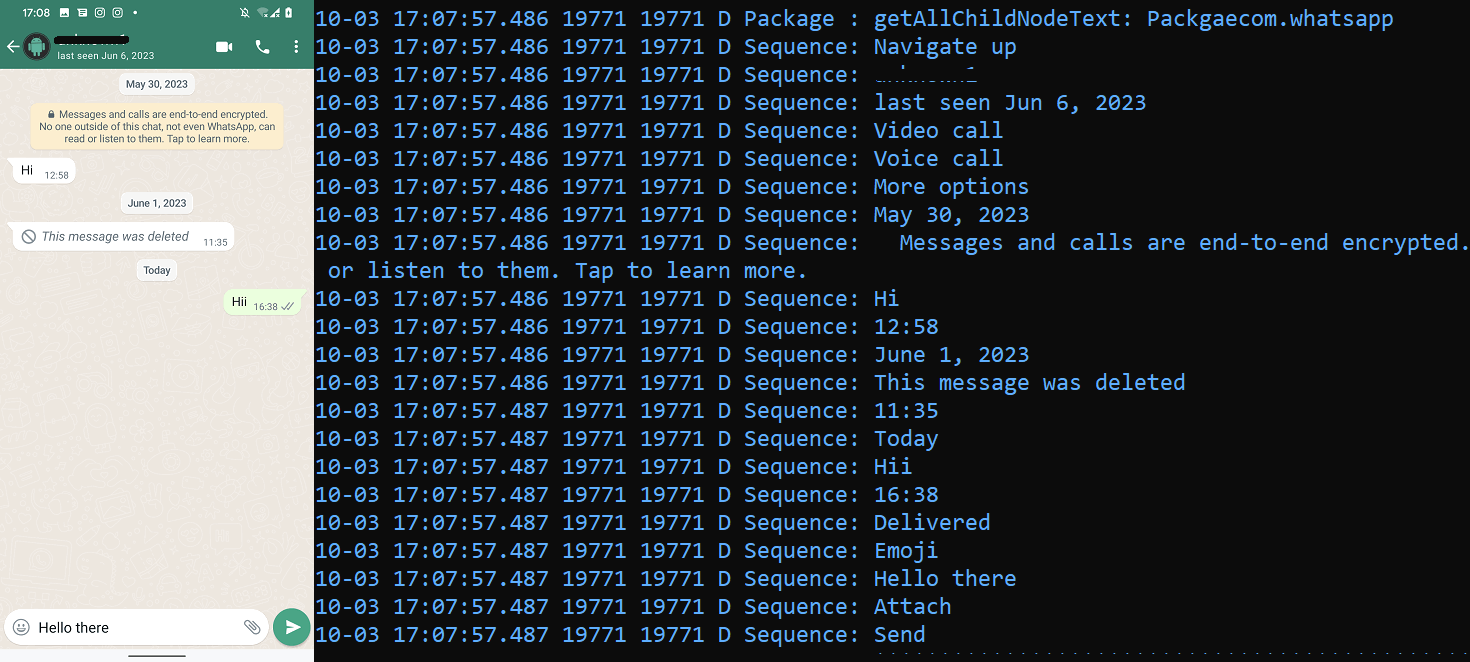
The power of VajraSpy lies in its modular nature and adaptability, while the extent of its spying capabilities is determined by the level of permissions it obtains on an infected device.
ESET concludes by advising that users should refrain from downloading obscure chat apps recommended by people they don't know, as this is a common and longstanding tactic cybercriminals employ to infiltrate devices.
While Google Play introduces new policies that make it harder for malware to hide in apps, threat actors continue to sneak their malicious apps onto the platform.
Previous attacks performed much better than this VajraSpy spyware campaign, such as an October adware campaign amassing 2 million installs.
More recently, it was discovered that the SpyLoan information-stealing malware was downloaded 12 million times from Google Play in 2023.
Update 2/2 - A Google spokesperson sent BleepingComputer the following comment:
We take security and privacy claims against apps seriously, and if we find that an app has violated our policies, we take appropriate action.
Users are protected by Google Play Protect, which can warn users of apps known to exhibit this malicious behavior on Android devices with Google Play Services, even when those apps come from sources outside of Play.
Update 2/24 - ESET has added the following note on the report:
This research covers specific apps and package names that have since been removed from the Google Play store.
Any similarly or identically named apps, such as MeetMe, that are still available on Google Play are purely coincidental and have not been affected.


Comments
Dr. Technical - 1 month ago
Once again, we are told that "certification" bestowed upon apps in the Google Play Store means nothing, and that apps can be allowed into the Store that contain malware, and the Google is fine with that, apparently.
Google's store is not alone in this problem, which plagues Apple's app store too.
This brings into question what procedures and methods are being used to screen applications seeking approval by these stores? What do the approval processes look for? With apps that get updated almost constantly, is scrutiny of the updates as rigorous as scrutiny of the initial approval? What checks are made to prevent transmittal of data from the device up to some mothership that goes far beyond whatever is truly necessary for the app to run properly?
And none of this goes to a real issue...What can we know about who is creating the apps? Where are they locataed? What professional training have they received? Are we looking at an app created by some teenager living in his mother's basement, or by a team of certified professional developers with years of experience and training? Don't we have a right to know that? Shouldn't an app be graded on how it meets with some professional standards?