South Korea's 'Korea Atomic Energy Research Institute' disclosed yesterday that their internal networks were hacked last month by North Korean threat actors using a VPN vulnerability.
The Korea Atomic Energy Research Institute, or KAERI, is the governement-sponsored institute for the research and application of nuclear power in South Korea.
The breach was first reported earlier this month when South Korean media Sisa Journal began covering the attack. At the time, KAERI initially confirmed and then denied that the attack occurred.
In a statement and press conference held yesterday by KAERI, the institute has officially confirmed the attack and apologized for attempting to cover up the incident.
Attributed to North Korean threat actors
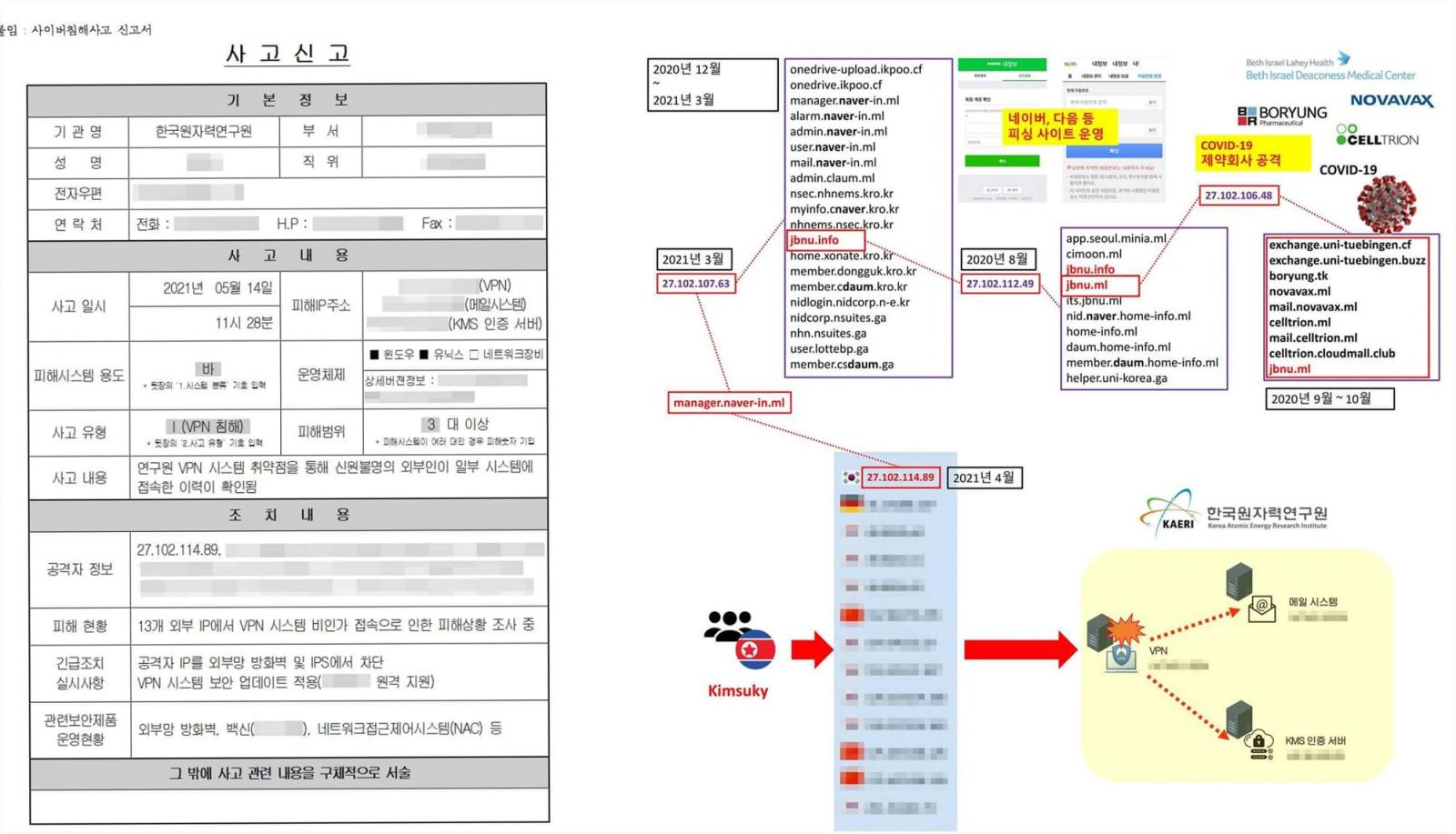
KAERI states the attack took place on June 14th after North Korean threat actors breached their internal network using a VPN vulnerability.
KAERI states that they have updated the undisclosed VPN device to fix the vulnerability. However, access logs show that thirteen different unauthorized IP addresses gained access to the internal network through the VPN.
One of these IP addresses is linked to a North Korean state-sponsored hacking group known as 'Kimsuky' that is believed to work under the North Korean Reconnaissance General Bureau intelligence agency.
In October 2020, CISA issued an alert on the Kimsuky APT group and stated that they are "likely tasked by the North Korean regime with a global intelligence gathering mission."
More recently, Malwarebytes has issued a report on how Kimsuky (aka Thallium, Black Banshee, and Velvet Chollima) has been actively targeting the South Korean government using the 'AppleSeed' backdoor in phishing attacks.
"One of the lures used by Kimsuky named “외교부 가판 2021-05-07” in Korean language translates to “Ministry of Foreign Affairs Edition 2021-05-07” which indicates that it has been designed to target the Ministry of Foreign Affairs of South Korea," explains Malwarebytes' report on the threat actor's recent activities.
"According to our collected data, we have identified that it is one entity of high interest for Kimsuky."
Malwarebytes states that Kimsuky has targeted other South Korean government agencies in recent phishing attacks, including:
- Ministry of Foreign Affairs, Republic of Korea 1st Secretary
- Ministry of Foreign Affairs, Republic of Korea 2nd Secretary
- Trade Minister
- Deputy Consul General at Korean Consulate General in Hong Kong
- International Atomic Energy Agency (IAEA) Nuclear Security Officer
- Ambassador of the Embassy of Sri Lanka to the State
- Ministry of Foreign Affairs and Trade counselor
KAERI states that they are still investigating the attack to confirm what information has been accessed.


Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now