
A previously unknown advanced threat actor tracked as 'Blackwood' is using sophisticated malware called NSPX30 in cyberespionage attacks against companies and individuals.
The adversary has been active since at least 2018 utilizing the NSPX30 malware, an implant with a codebase rooted in a simple backdoor from 2005, following adversary-in-the-middle (AitM) attacks.
Researchers at cybersecurity company ESET discovered Blackwood and the NSPX30 implant in a campaign in 2020 and believe that the group's activities align with Chinese state interests.
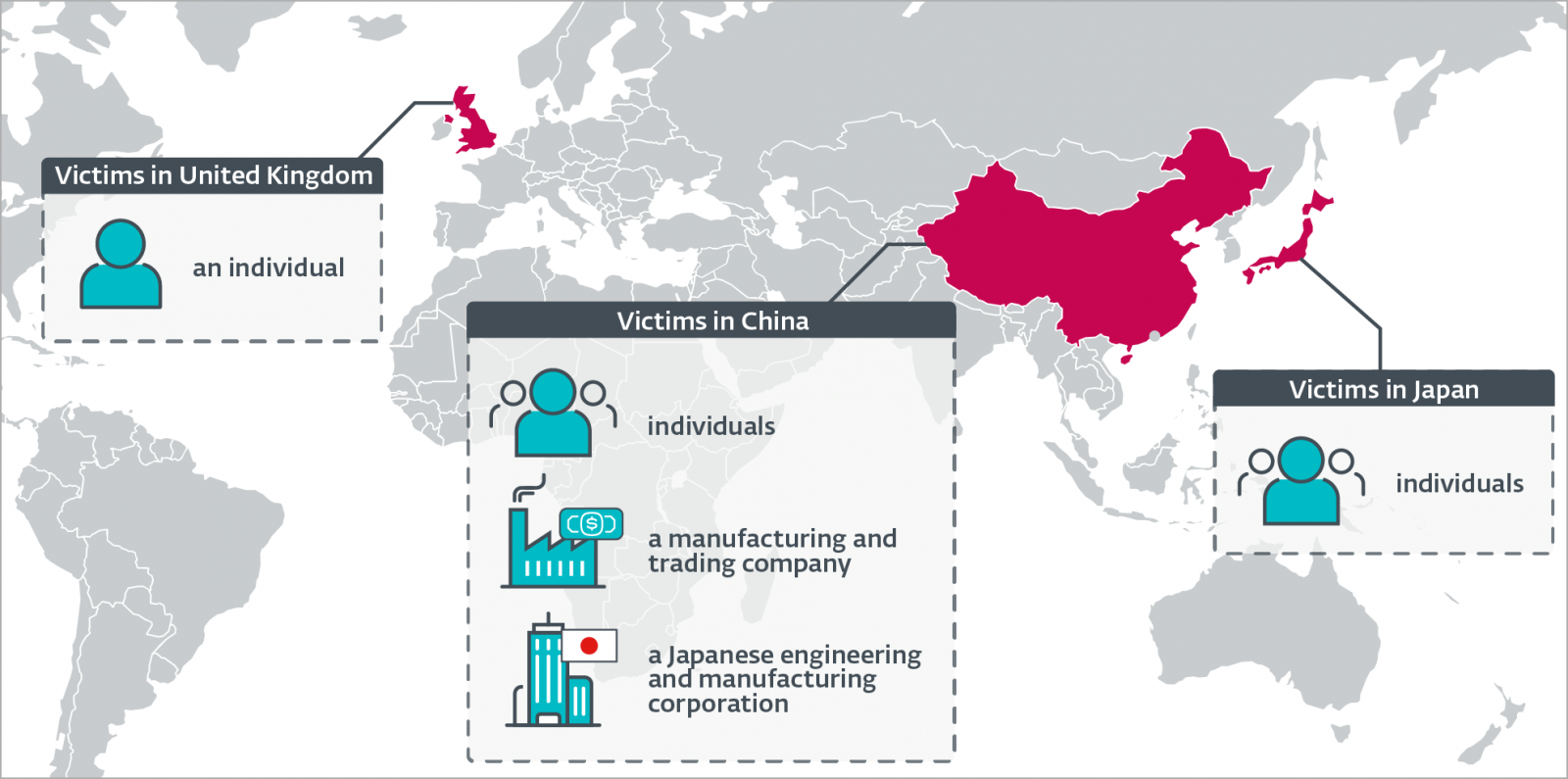
Blackwood's targets are in China, Japan, and the United Kingdom and delivered the malware through the update mechanisms of legitimate software like WPS Office (office suite), the Tencent QQ instant messaging platform, and the Sogou Pinyin document editor.
According to the researchers, the threat actor carries out AitM attacks and intercepts traffic generated by NSPX30 to conceal its activities and hide its command and control (C2) servers.
ESET also notes that Blackwood possibly shares access with other Chinese APT groups, as it observed the system of one company being targeted by toolkits associated with multiple actors, e.g. Evasive Panda, LuoYu, and LittleBear.
NSPX30 origin and evolution
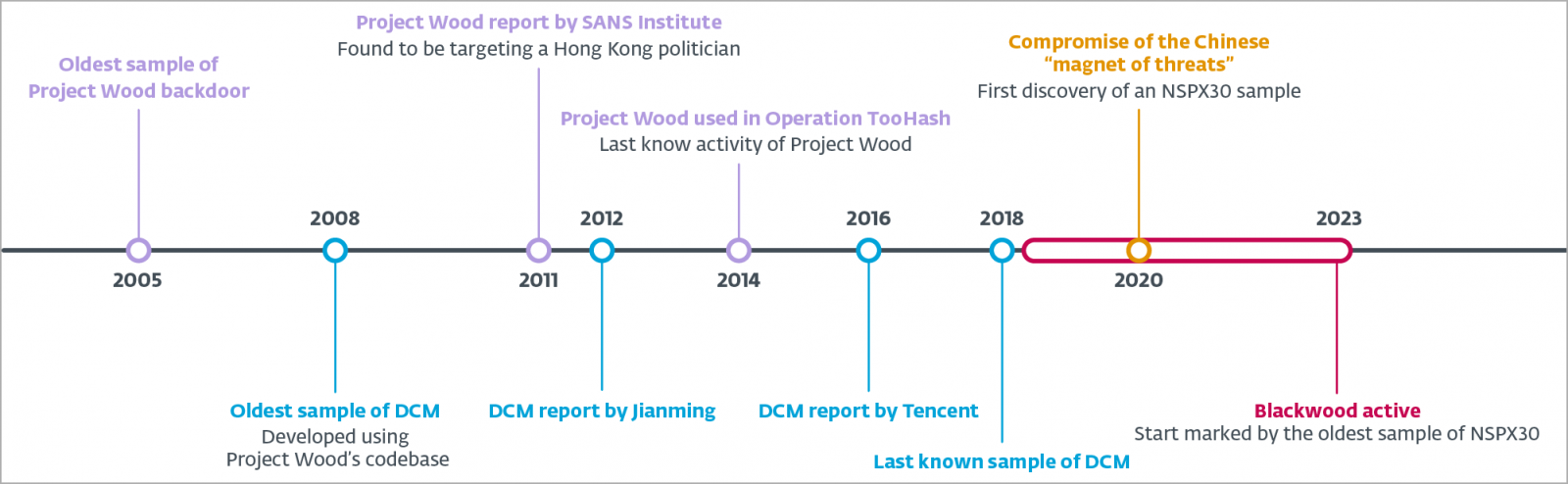
NSPX30 is a sophisticated implant based on code from a backdoor in 2005 named 'Project Wood' that had elementary capabilities to collect system data, keylogging, and taking screenshots.
Among other implants emerging from Project Wood was DCM (Dark Specter), first seen in the wild in 2008, featuring multiple functional enhancements.
ESET believes that NSPX30 evolved from DCM with the first known sample of the malware documented in 2018.
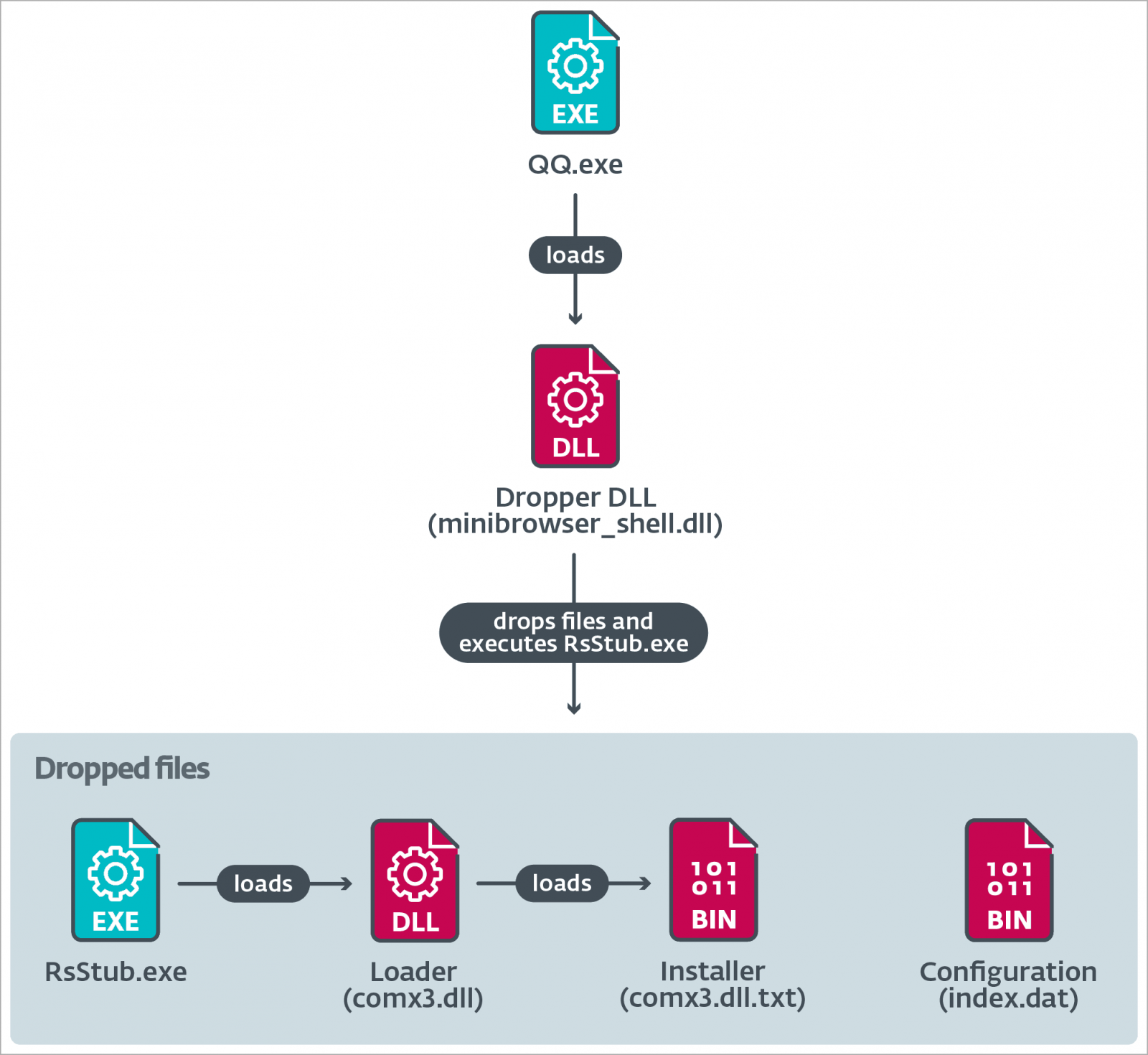
Unlike its predecessors, NSPX30 is characterized by its multistage architecture, which includes components like a dropper, a DLL installer with extensive UAC bypassing capabilities, a loader, an orchestrator, and a backdoor, each with its own set of plugins.
NSPX30 demonstrates significant technical advancement, with capabilities for packet interception to hide its infrastructure, allowing it to operate covertly. It also has mechanisms that add it onto allowlists of Chinese anti-malware tools to evade detection.
The primary function of NSPX30 is to collect information from the breached system, including files, screenshots, key presses, hardware and network data, and credentials.
The backdoor can also steal chat logs and contact lists from Tencent QQ, WeChat, Telegram, Skype, CloudChat, RaidCall, YY, and AliWangWang.
The backdoor can also terminate processes by PID, create a reverse shell, move files to specified paths, or uninstall itself from the infected system.
AitM attacks
A notable aspect of Blackwood's activities is the ability to deliver NSPX30 by hijacking update requests made by legitimate software, including Tencent QQ, WPS Office, and Sogou Pinyin.
This is different from a supply-chain compromise, though, because Blackwood intercepts unencrypted HTTP communication between the victim's system and the update server and intervenes to deliver the implant instead.
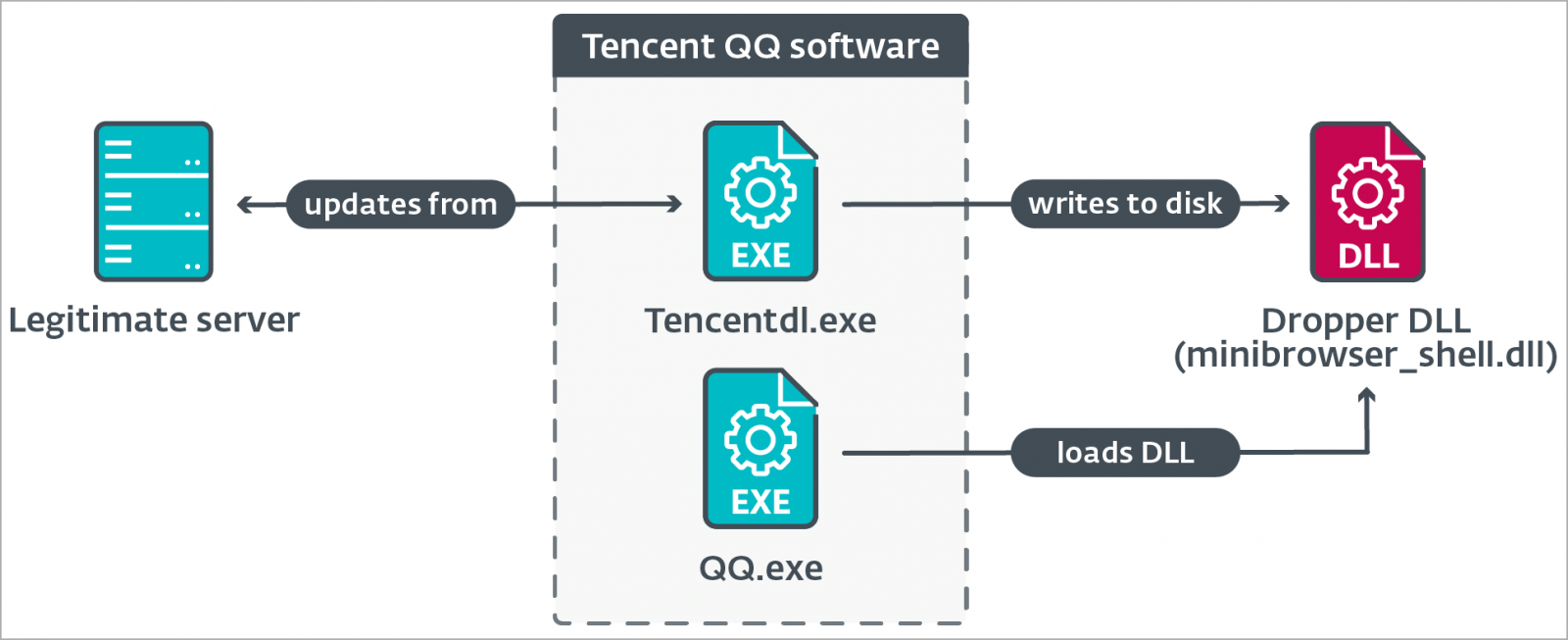
The exact mechanism that enables Blackwood to intercept that traffic in the first place is unknown. ESET speculates it might be possible by using an implant in the networks of the targets, possibly on vulnerable appliances such as routers or gateways.
Based on their analysis, the researchers believe that the original backdoor at the root of the evolution of the NSPX30 custom implant seems to have been developed by skilled malware developers.
ESET's report provides ample technical details about the malware and how it works and also includes a list of indicators of compromise that defenders can use to protect their environment.


Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now