
The alleged source code for the third iteration of the Knight ransomware is being offered for sale to a single buyer on a hacker forum by a representative of the operation.
Knight ransomware launched at the end of July 2023 as a re-brand of the Cyclops operation, targeting Windows, macOS, and Linux/ESXi systems.
It gained some traction because it provided info-stealers and a ‘lite’ version of its encryptor for lower-tier affiliates that attacked smaller organizations.
Threat analysts at cyber-intelligence firm KELA spotted the advertisement two days ago posted on RAMP forums by someone using the alias Cyclops, known as a representative of the Knight ransomware gang.
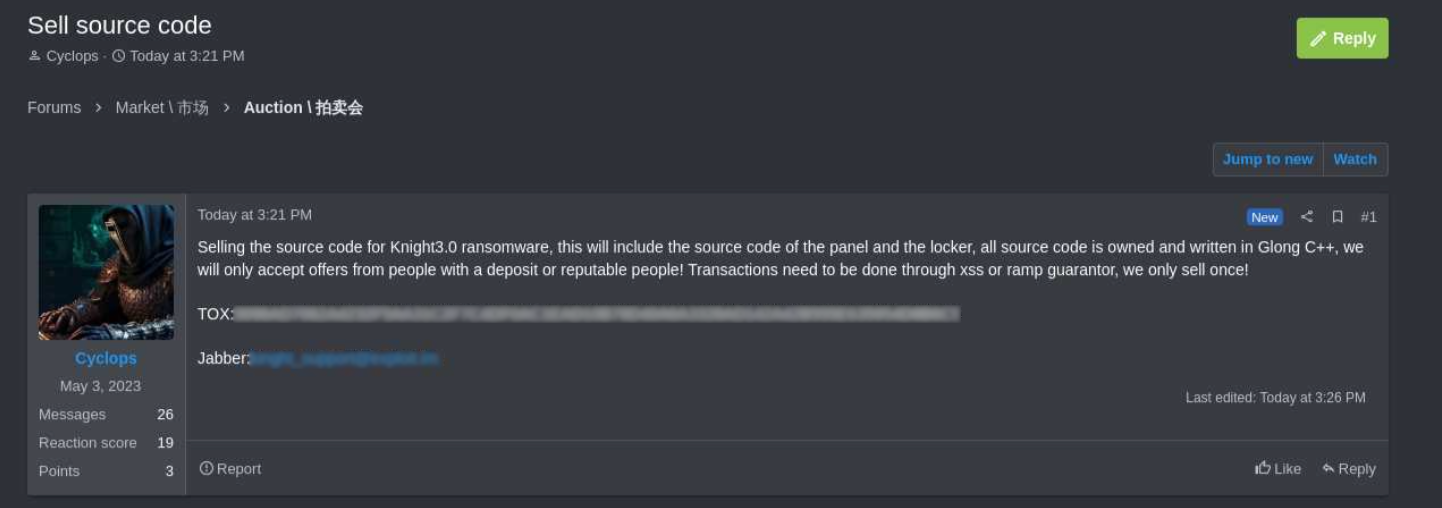
“Selling the source code for Knight 3.0 ransomware, this will include the source code of the panel and the locker, all source code is owned and written in Glong C++,” says Cyclops in the post.
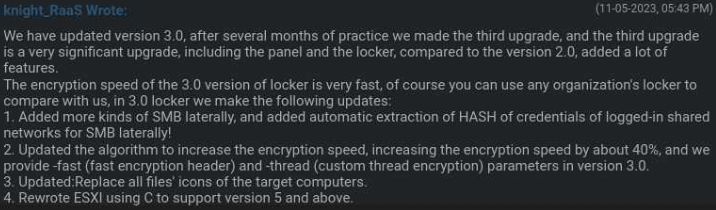
Version 3.0 of Knight's locker was released on November 5, 2023, with 40% faster encryption, a re-written ESXi module to add support for more recent versions of the hypervisor, and various other improvements.
The threat actor did not specify a price but emphasized that the source code would only be sold to a single buyer, preserving its value as a private tool.
Cyclops said they would prioritize reputable users with a deposit and that the purchase would be conducted through a transaction guarantor either on RAMP or XSS hacker forum.
The seller has posted contact addresses for Jabber and TOX messaging services for potential buyers to reach out and negotiate a final deal.
KELA told BleepingComputer that the Jabber is new but the TOX ID listed on the forum post is known and previously associated with Knight, which adds legitimacy to the sale.
The reason behind selling the source code for Knight ransomware remains unclear but KELA’s dark web monitoring tools have logged no activities from Knight’s representatives on various forums since December 2023.
Also, the ransomware operation’s victim extortion portal is currently offline, the last victim being listed on February 8. Since July 2023, Knight claimed to have breached 50 organizations.
Based on the details from KELA, the Knight ransomware operation appears to have gone inactive for a while now, so it’s possible that the group is looking to close shop and sell their assets.


Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now