
A Chinese state-sponsored hacking group named "Camaro Dragon" infects residential TP-Link routers with a custom "Horse Shell" malware used to attack European foreign affairs organizations.
The backdoor malware is deployed in a custom and malicious firmware designed specifically for TP-Link routers so that the hackers can launch attacks appearing to originate from residential networks.
"It is worth noting that this kind of attack is not aimed specifically at sensitive networks, but rather at regular residential and home networks," explains the Check Point report.
"Therefore, infecting a home router does not necessarily mean that the homeowner was a specific target, but rather that their device was merely a means to an end for the attackers."
The deployed malware allows the threat actors full access to the device, including running shell commands, uploading and downloading files, and using it as a SOCKS proxy to relay communication between devices.
The Horse Shell TP-Link firmware implant was discovered by Check Point Research in January 2023, who says the hackers' activity overlaps with the Chinese "Mustang Panda" hacking group recently detailed in Avast and ESET reports.
Check Point tracks this activity separately using the "Camaro Dragon" name for the activity cluster despite the similarities and considerable overlap with Mustang Panda.
The attribution was made based on attackers' server IP addresses, requests featuring hard-coded HTTP headers found on various Chinese websites, many typos in the binary code that show the author isn't a native English speaker, and functional similarities of the trojan with the APT31 "Pakdoor" router implant.
TP-Link firmware implant
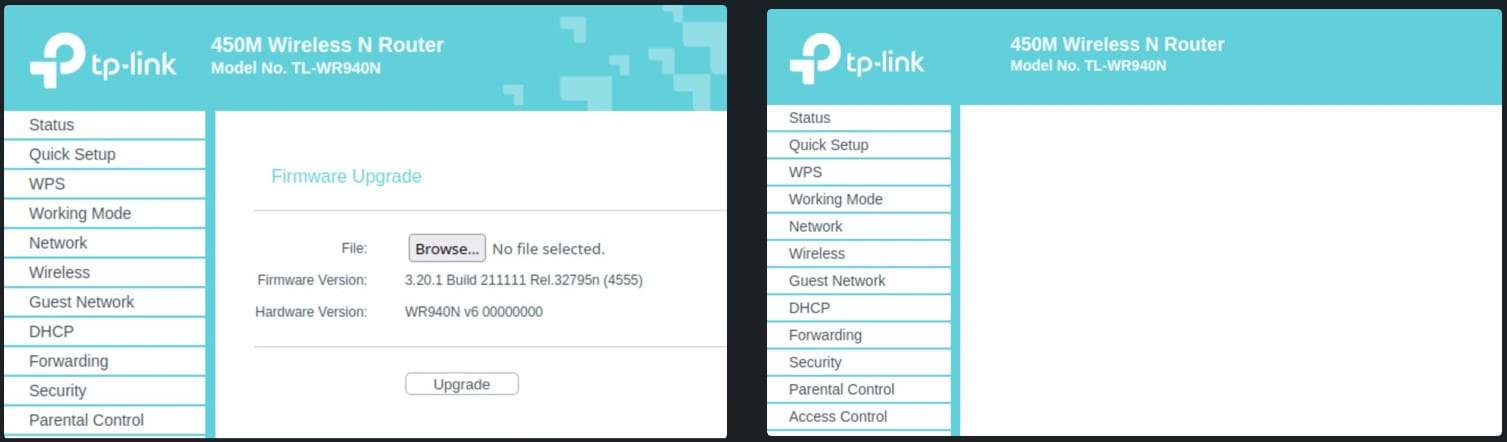
While Check Point has not determined how the attackers infect TP-Link routers with the malicious firmware image, they said it could be by exploiting a vulnerability or brute-forcing the administrator's credentials.
Once a threat actor gains admin access to the management interface, they can remotely update the device with the custom firmware image.
Through investigation, Check Point found two samples of trojanized firmware images for TP-Link routers, both containing extensive modifications and file additions.
Check Point compared the malicious TP-Link firmware with a legitimate version and found that the kernel and uBoot sections were the same. However, the malicious firmware utilized a custom SquashFS filesystem that contained additional malicious file components that are part of the Horse Shell backdoor malware implant.
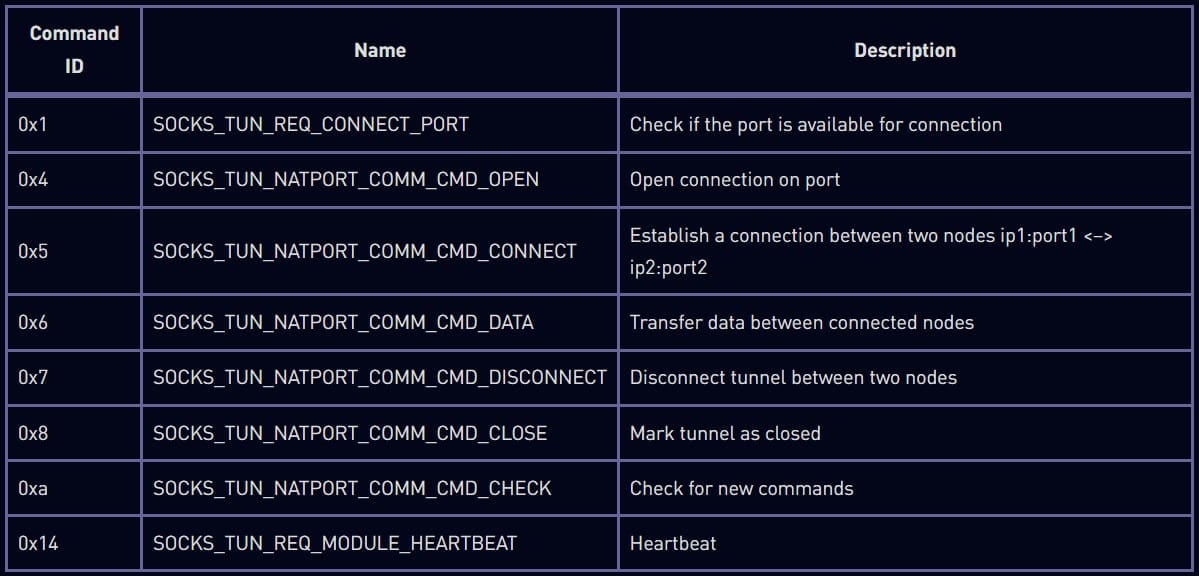
"Parts of it are internally named Horse Shell so we use it to name the implant as a whole. The implant provides the attacker with 3 main functionalities: remote shell, file transfer, and tunneling," explains Check Point.
The firmware also modifies the management web panel, preventing the device's owner from flashing a new firmware image for the router and ensuring the persistence of the infection.
The Horse Shell backdoor
When the Horse Shell backdoor implant is initialized, it will instruct the OS not to terminate its process when the SIGPIPE, SIGINT, or SIGABRT commands are issued, and to be converted into a daemon to run in the background.
The backdoor will then connect to the command and control (C2) server to send the victim's machine profile, including the user name, OS version, time, device information, IP address, MAC address, and supported implant features.
Horse Shell will now quietly run in the background waiting for one of the following three commands:
- Start a remote shell providing the threat actors full access to the compromised device.
- Perform file transfer activities, including uploading and downloading, basic file manipulation, and directory enumeration.
- Start tunneling to obfuscate the origin and destination of the network traffic and hide the C2 server address.
The researchers say the Horse Shell firmware implant is firmware-agnostic, so it could theoretically work in firmware images for other routers by different vendors.
It's not surprising to see state-sponsored hackers targeting poorly secured routers, often targeted by botnets for DDoS attacks or crypto-mining operations. This is because routers are often overlooked when implementing security measures and can act as a stealthy launchpad for attacks, obfuscating the attacker's origin.
Users are advised to apply the latest firmware update for their router model to patch any existing vulnerabilities and change the default admin password to something strong. However, even more critical, disable remote access to the device's admin panel and make it only accessible from the local network.
A recurring theme
Edge network devices have become a popular target for state-sponsored threat actors, with Chinese hackers previously targeting Fortinet VPN and SonicWall SMA routers with custom firmware implants.
More recently, the UK NCSC and US CISA cybersecurity agencies warned that Russian state-sponsored threat actors were also breaching Cisco routers to install custom malware.
As these devices do not commonly support EDR (Endpoint Detection and Response) security solutions, threat actors can use them to steal data, spread laterally, and conduct further attacks with less opportunity for detection.
"There's a recurring theme of continued China-nexus cyber espionage focus on network appliances, IOT devices, etc. that don't support EDR solutions," Mandiant CTO Charles Carmakal told BleepingComputer.
For this reason, it is vital for network admins to install all available security patches on edge devices as soon as they become available and not publicly expose management consoles.


Comments
johnlsenchak - 9 months ago
I wouldn't recommend TP-Link routers to anyone
bradleyross - 9 months ago
My personal feeling is that there is too much trust in the ability of routers to resist attacks and therefore be placed into a state where they can be used to carry out massive attacks. The idea that routers and switches can be configured to provide virtual networks to halt malicious attacks means that they are also inserting the capability to be used for attacking systems. I don't trust patches or the competence of vendors, especially after the episode with the RSA SecurID tokens. When I look at high-end systems such as Cisco, they seem to be touting the ability for a single manager to test packets going between units and set privileges for devices. The literature all seems to say: "You can trust me, so don't worry". I don't trust anyone who has that attitude, and I worry a lot. The protections they put on the systems just seem to make them more vulnerable to competent actors. And it seems like all of the hacking organizations are getting advice from people who know things.
queueue - 9 months ago
I have trouble reading so I probably missed the obvious, but can someone explain:
"Users are advised to apply the latest firmware update for their router model to patch any existing vulnerabilities.."
and
"The firmware also modifies the management web panel, preventing the device's owner from flashing a new firmware image for the router and ensuring the persistence of the infection."
Also, when was the last time anyone got a meaningful update for their router? My last TP-Link router received ONE update and it was to correct a typo that they made. But I'm sure typos are everyone's number one pet peeve and would rather have 'eguipment' fixed than get security vulnerability updates.
Bill_Toulas - 9 months ago
Hello,
The recommendation to update to the latest firmware version was meant as a protective measure, not as a post-infection solution.
M4C - 9 months ago
Not necessarily. Most routers have a button to reset them back to factory defaults. It is possible that a user with an infected router could perform the reset then update it with official firmware. I dont know if it would work but I would try it before trashing the router. Don’t take that as official advice it’s just a suggestion.