
The popular KeePass password manager is vulnerable to extracting the master password from the application's memory, allowing attackers who compromise a device to retrieve the password even with the database is locked.
The issue was discovered by a security researcher known as 'vdohney,' who published a proof-of-concept tool allowing attackers to extract the KeePass master password from memory as a proof-of-concept (PoC).
Password managers allow users to create unique passwords for every online account and store the credentials in an easy-to-search database, or password vault, so you do not have to remember each one. However, to properly secure this password vault, users must remember the one master password used to unlock it and access stored credentials.
This master password encrypts the KeePass password database, preventing it from being opened or read without first entering the password. However, once that master password is compromised, a threat actor can access all the credentials stored in the database.
Therefore, for a password manager to be properly secured, it is critical that users guard the master password and not share it with anyone else.
A new KeePass vulnerability tracked as CVE-2023-3278 makes it possible to recover the KeePass master password, apart from the first one or two characters, in cleartext form, regardless of whether the KeePass workspace is locked, or possibly, even if the program is closed.
"KeePass Master Password Dumper is a simple proof-of-concept tool used to dump the master password from KeePass's memory. Apart from the first password character, it is mostly able to recover the password in plaintext," warns the security researcher on the GitHub page for the exploit tool.
"No code execution on the target system is required, just a memory dump. It doesn't matter where the memory comes from - can be the process dump, swap file (pagefile.sys), hibernation file (hiberfil.sys) or RAM dump of the entire system. It doesn't matter whether or not the workspace is locked."
The flaw exists because the software uses a custom password entry box named "SecureTextBoxEx," which leaves traces of each character the user types in the memory.
"KeePass 2.X uses a custom-developed text box for password entry, SecureTextBoxEx. This text box is not only used for the master password entry, but in other places in KeePass as well, like password edit boxes (so the attack can also be used to recover their contents)," explains vdohney.
The vulnerability impacts the latest version of KeePass, 2.53.1, and as the program is open-source, any project forks are likely affected.
KeePass 1.X, KeePassXC, and Strongbox do not appear to be impacted by CVE-2023-32784, according to the developer of the password dumping tool.
Also, while the PoC was tested on Windows, the exploit should also work for Linux and macOS, with some modifications, as the problem isn't specific to the OS but how KeePass handles user input.
Source: vdohney
Easy to exploit
Since memory dumps must be retrieved for the KeePass master password to be recovered, the exploitation of CVE-2023-32784 requires physical access or malware infection on the target machine.
However, information-stealing malware could quickly check if KeePass exists on a computer or is running, and if so, dump the program's memory and send it and the KeePass database back to the attacker for offline retrieval of the cleartext password from the memory dump.
BleepingComputer tested vdohney's 'keepass-password-dumper' tool by installing KeePass on a test device and creating a new database with the master password 'password123,' as shown below.
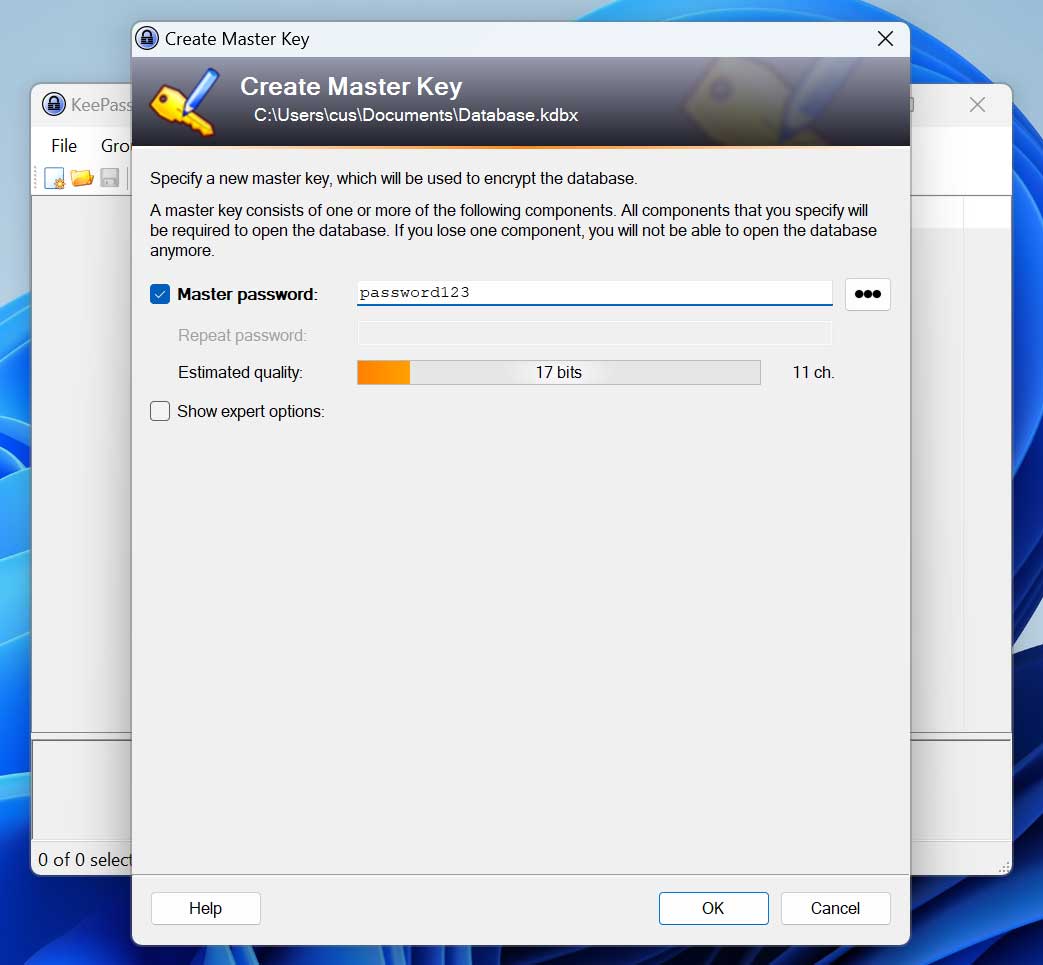
Source: BleepingComputer
We then locked our KeePass workspace, which prevents access to it unless you enter the master password again.
In our tests, you can use Process Explorer to dump the memory of the KeePass project, but it requires a full memory dump, and not a minidump, to work correctly. No elevated privileges are needed to dump the processes' memory.
After compiling vdohney's tool using Visual Studio, we executed it against our memory dump, and it quickly recovered most of our cleartext password, with just the first two letters missing.
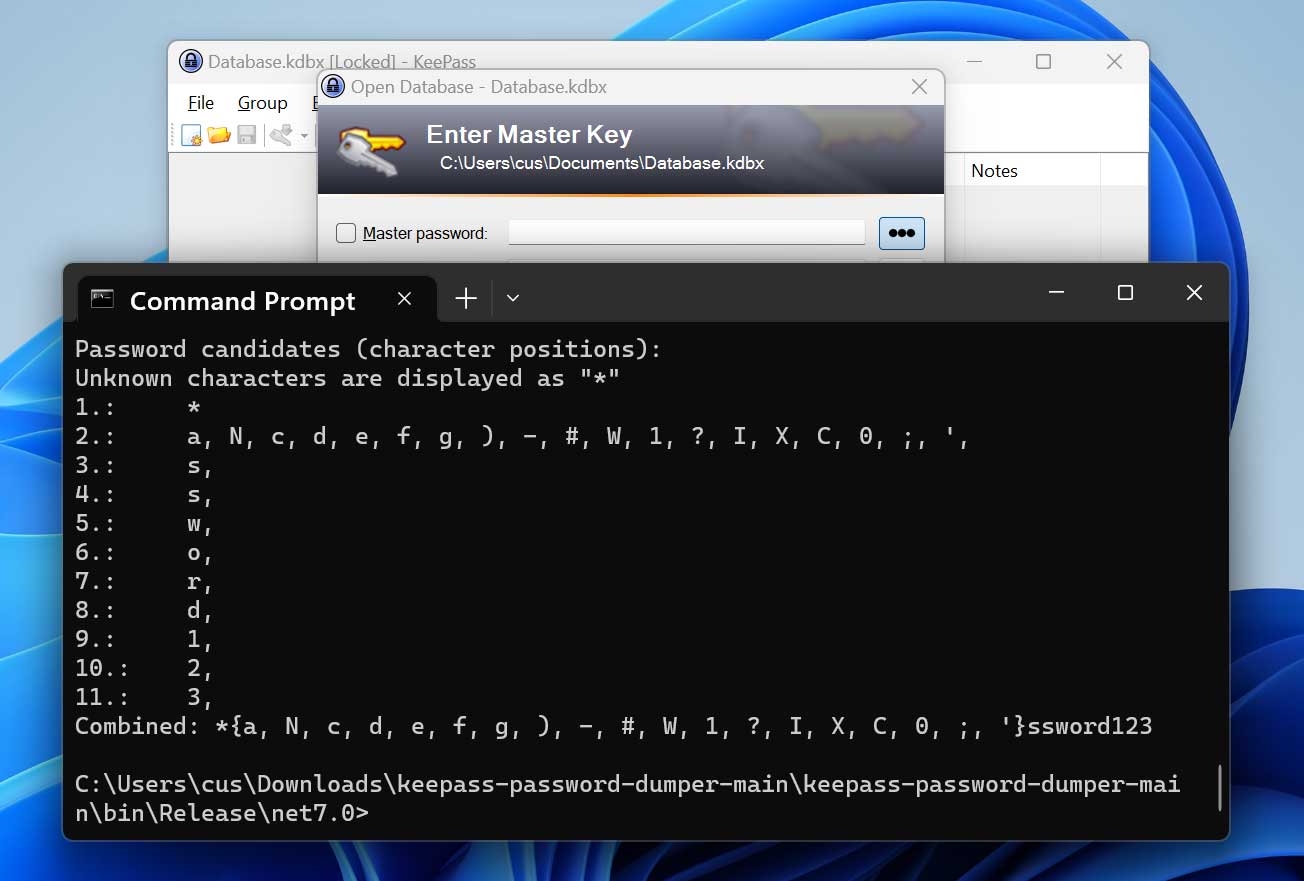
Source: BleepingComputer
While this is not the complete password, determining what characters are missing would be fairly easy.
The researcher also warns that master passwords used in the past can remain in memory, so they can be retrieved even if KeePass is no longer running on the breached computer.
Fix coming soon
The developer of KeePass, Dominik Reichl, received the bug report and promised to roll out a fix for CVE-2023-32784 on version 2.54, expected sometime in July 2023.
However, Reichl told BleepingComputer that KeePass version 2.54 is more likely to be released to users in about two weeks, so it should be out by early June.
Based on a discussion where Reichl developed his thoughts on the security flaw and the potential mitigation strategies, two security enhancements are mentioned for the upcoming KeePass version:
- Perform direct API calls for getting/setting the text of the text box, avoiding the creation of managed strings in memory that can leak secrets.
- Create dummy fragments containing random characters in the process memory that will have approximately the same length as the user's master password, obfuscating the real key.
KeePass 2.54 for Windows will have both, while macOS and Linux versions will only get the second enhancement.
The developer has released a test version with the new security enhancements that mitigate the issue, so those who can accept unstable behavior can source it from here.
The creator of the PoC has confirmed that he can no longer reproduce the attack with the two security enhancements in place, so the fix appears to be effective.
Even after the new version is released, the master password may still be stored in memory files. The researcher warns that to be 100% safe that it is not lurking on the system, you would need to delete your system's swap and hibernation files, format your hard drive using the "overwrite data" mode to prevent data recovery, and do a fresh OS install.
For most, though, restarting the computer, clearing your swap file and hibernation files, and not using KeePass until the new version is released are reasonable safety measures for the time being.
Even then, for the best protection, be super vigilant about not downloading programs from untrusted sites and beware of phishing attacks that may infect your devices, giving threat actors remote access to your device and your KeePass database.


Comments
GT500 - 9 months ago
Why was the vulnerability made public before a stable release of KeePass that contained a mitigation was available? At first glance this does not seem like responsible vulnerability reporting to me.
EndangeredPootisBird - 9 months ago
A better question is, why release PoC's at all? It's like the Penetration Testing industry, it does nothing but aid cybercriminals.
dusselduss - 9 months ago
What are you guys even talking about? The PoC was posted in an exclusive forum and the dev of KeePass was the first answer to the thread.
Are you really asking why PoCs are created? How do we know a vulnerability is real if we do not find PoCs for it? If it wasnt proven to work, why would the developer bring a fix?
These two comments just showed you guys really need to learn about PoC, vulnerability reporting and the like.
GT500 - 9 months ago
Obviously PoC's are important proof that vulnerabilities exist, and they help developers and other security experts to validate vulnerability reports. Please don't misunderstand my comment above to have anything to do with PoC's.
As for the reporting, it is standard practice not to make a vulnerability publicly known until a fix is available and in wide circulation. The only times when this practice is not held to are when a developer/company refuse to recognize or patch a legitimate security issue, then after some time or attempting to work with the developer/company in question some security researchers/pen testers will release vulnerability details and PoC's publicly to warn users about the danger and hopefully motive the developer/company to fix the issue. Since this does not appear to be one of those cases (the developer responded and is working on a fix) I have to wonder why information about the vulnerability was made public at all.
EndangeredPootisBird - 9 months ago
PoC's should never be made available to everyone to see, they should be offered exclusively to businesses who request it. We have seen that it does nothing but cause more breaches rather than prevents them, like penetration testing and tools.
Wannabetech1 - 9 months ago
Can you explain this? I thought Pen testing was a way to test the security of systems?
Keeping in mind that I'm just a "wannabe", please keep your answer simple if possible.
Instead of "KISS", please make it KISFS(Keep It Simple For Stupid). I'm stupid.
GT500 - 9 months ago
Pen testing (short for penetration testing) is the name of a security practice where testing is done to find vulnerabilities. Its an essential process, and the companies having big security breaches are usually failing to do it (or failing to do it properly, or failing to listen to their pen testers, etc). It usually involves testing networks, web applications, and websites using a suite of tools (mostly open source and community maintained) running on platforms like Kali Linux. There are a series of best practices that are usually followed, as well as regulations that need to be followed, to ensure that it is done properly without compromising security and/or privacy (for instance something like publicly documenting a vulnerability before it is patched could lead to exploitation of the vulnerability by criminals or nation state threat actors/hackers).
Brok - 9 months ago
'Run as Administrator' KeePass2.exe should help as a temporary measure, makes process Integrity level High and not every notepad will be able to read his memory