
A vulnerability impacting Fortinet VPNs is being exploited by a new human-operated ransomware strain known as Cring to breach and encrypt industrial sector companies' networks.
Cring ransomware (also known as Crypt3r, Vjiszy1lo, Ghost, Phantom) was discovered by Amigo_A in January and spotted by the CSIRT team of Swiss telecommunications provider Swisscom.
The Cring operators drop customized Mimikatz samples, followed by CobaltStrike after gaining initial access and deploy the ransomware payloads by downloading using the legitimate Windows CertUtil certificate manager to bypass security software.
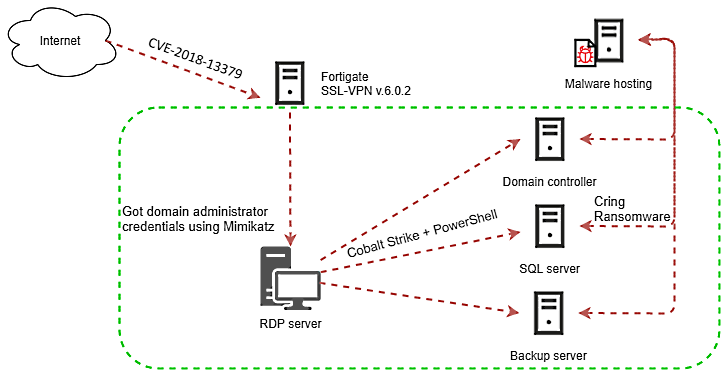
As Kaspersky researchers revealed in a report published today, the attackers exploit Internet-exposed Fortigate SSL VPN servers unpatched against the CVE-2018-13379 vulnerability, which allows them to breach their targets' network.
"Victims of these attacks include industrial enterprises in European countries," Kaspersky researchers said.
"At least in one case, an attack of the ransomware resulted in a temporary shutdown of the industrial process due to servers used to control the industrial process becoming encrypted."
Cring ransomware attacks
From the Fortinet VPN appliance, Cring operators move laterally on the targets' enterprise network stealing Windows user credentials using Mimikatz to gain control of the domain administrator account.
The ransomware payloads are then delivered to devices on the victims' networks using the Cobalt Strike threat emulation framework deployed using a malicious PowerShell script.
The ransomware encrypts only specific files on the compromised devices using strong encryption algorithms (RSA-8192 + AES-128) after removing backup files and killing Microsoft Office and Oracle Database processes.
It then drops ransom notes named !!!!!readme.rtf and deReadMe!!!.txt warning the victims that their network was encrypted and that they need to hurry to pay the ransom because the decryption key will not be kept indefinitely.
Sorry, your network is encrypted, and most files are encrypted using special technology. The file cannot be recovered by any security company. If you do not believe that you can even consult a security company, your answer will be that you need to pay the corresponding fees, but we have a good reputation. After receiving the corresponding fee, we will immediately send the decryption program and KEY. You can contact us to get two file decryption services, and then you will get all decryption services after paying our fee, usually the cost is about 2 bitcoins.
Contact: eternalnightmare@tutanota.com qkhooks0708@protonmail.com
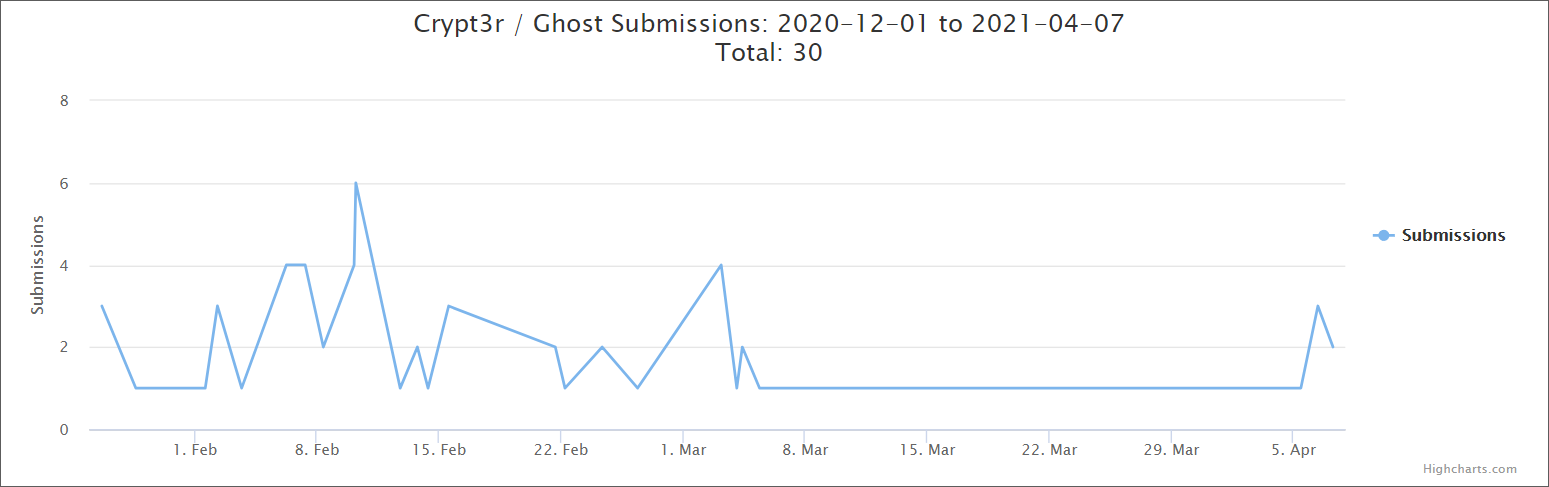
Victims have been using the ID-Ransomware service to check if their systems were hit by Cring ransomware since the operation first surfaced in December 2020.
30 Cring ransomware samples have been submitted so far, with at least one per day since the end of January.
Indicators of compromise (IOCs), including malware sample hashes, C2 server IP addresses, and malware-hosting server addresses, are available at the end of Kaspersky's report.
Fortinet products targeted by APT and cybercrime groups
The Federal Bureau of Investigation (FBI) and the Cybersecurity and Infrastructure Security Agency (CISA) warned earlier this week of advanced persistent threat (APT) actors scanning for Fortinet SSL VPN appliances vulnerable to CVE-2018-13379 exploits.
The joint advisory also warns of attackers enumerating servers unpatched against CVE-2020-12812 and CVE-2019-5591.
As shown by previous campaigns, any servers compromised during these infiltration attempts might be used in future attacks as initial access vectors to breach government or commercial organizations' networks.
"The APT actors may be using any or all of these CVEs to gain access to networks across multiple critical infrastructure sectors to gain access to key networks as pre-positioning for follow-on data exfiltration or data encryption attacks," the agencies warned.
"APT actors have historically exploited critical vulnerabilities to conduct distributed denial-of-service (DDoS) attacks, ransomware attacks, structured query language (SQL) injection attacks, spearphishing campaigns, website defacements, and disinformation campaigns."
State hackers abused the CVE-2018-13379 vulnerability in the past to compromise U.S. election support systems reachable over the Internet.
Fortinet also warned customers to patch their appliances against the CVE-2018-13379 in August 2019, July 2020, November 2020, and again in April 2021.
"The security of our customers is our first priority. CVE-2018-13379 is an old vulnerability resolved in May 2019," Fortinet told BleepingComputer earlier this week. "If customers have not done so, we urge them to immediately implement the upgrade and mitigations."


Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now