
Security researchers found that infections with high-profile spyware Pegasus, Reign, and Predator could be discovered on compromised Apple mobile devices by checking Shutdown.log, a system log file that stores reboot events.
Kaspersky released Python scripts to help automate the process of analyzing the Shutdown.log file and recognize potential signs of malware infection in a way that is easy to evaluate.
Shutdown.log is written when upon rebooting the device and registers the time a process needs to terminate and their identifier (PID).
iShutdown scripts
Malware that has a measurable effect on device reboot due to the process injection and manipulation it performs, leaves digital forensic artifacts that validate the compromise.
Compared to standard techniques like examining an encrypted iOS backup or network traffic, the Shutdown.log file provides a much easier analysis method, the researchers say.
Kaspersky has published three Python scripts called iShutdown that allow researchers check reboot data from the iOS shutdown log file:
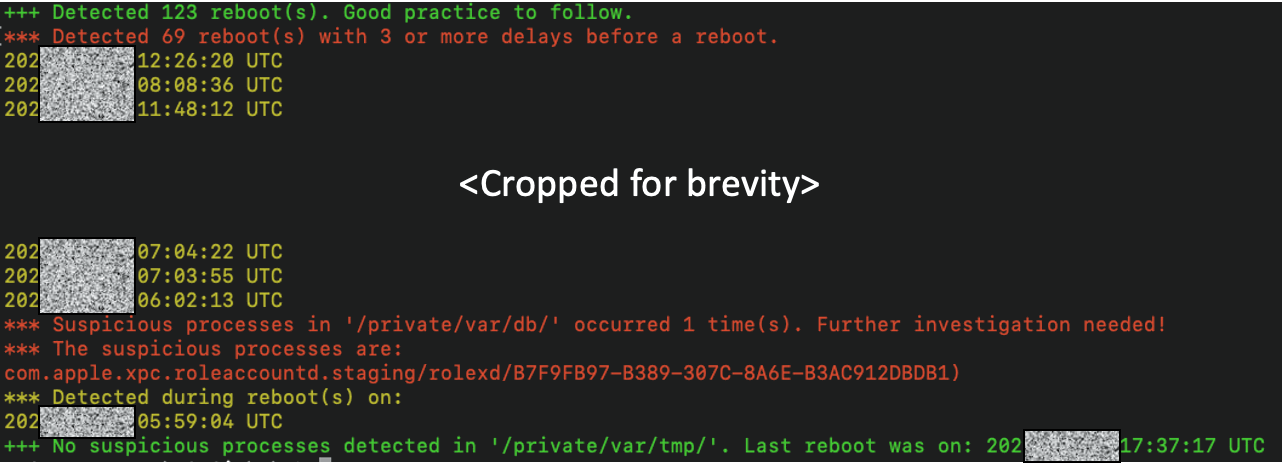
- iShutdown_detect.py - analyzes the Sysdiagnose archive that contains the log file
- iShutdown_parse.py - extracts the Shutdown.log artifacts from the tar archive
- iShutdown_stats.py - extracts reboot stats from the log file
Because the Shutdown.log file can only write data containing signs of infection if a reboot is performed after the compromise, Kaspersky recommends restarting the device infection often.
"How often, you may ask? Well, it depends! It depends on the user’s threat profile; every few hours, every day, or perhaps around “important events”; we’ll leave this as an open-ended question" - Kaspersky
Kaspersky’s GitHub repository contains instructions on how to use the Python scripts, and also example outputs. However, some familiarity with Python, iOS, terminal output, and malware indicators is required to evaluate the results properly.
Sysdiagnose files are 200-400MB .tar.gz archives used for troubleshooting iOS and iPadOS devices, containing information about software behavior, network communications, and more.
Kaspersky initially used the method to analyze iPhones infected with Pegasus spyware and received the infection indicator in the log, which was confirmed using the MVT tool developed by Amnesty International.
"Since we confirmed the consistency of this behavior with the other Pegasus infections we analyzed, we believe it will serve as a reliable forensic artifact to support infection analysis" - Kaspersky
The researchers note that their method fails if the user doesn't reboot the device on the day of the infection. Another observation is that the log file registers when a reboot is delayed, such as in the case of a Pegasus-related process that prevents the procedure.
While this can happen on non-infected phones, Kaspersky researchers believe that more than four delays, which is considered excessive, are a log anomaly that should be investigated.
When testing the method on an iPhone infected with Reign spyware, the researchers noticed that the malware execution originated from “/private/var/db/,” the same path as in the case of Pegasus.
A similar path visible in the Shurdown log file is also often used by the Predator spyware that targeted lawmakers and journalists.
Based on this, Kaspersky researchers believe that using the "log file may be able to help identify infections by these malware families," provided that the target reboots their phone frequently enough.


Comments
DIMMReaper_ - 1 month ago
"The researchers note that their method fails if the user doesn't reboot the device on the day of the infection"
So basically this is worthless and up to chance...