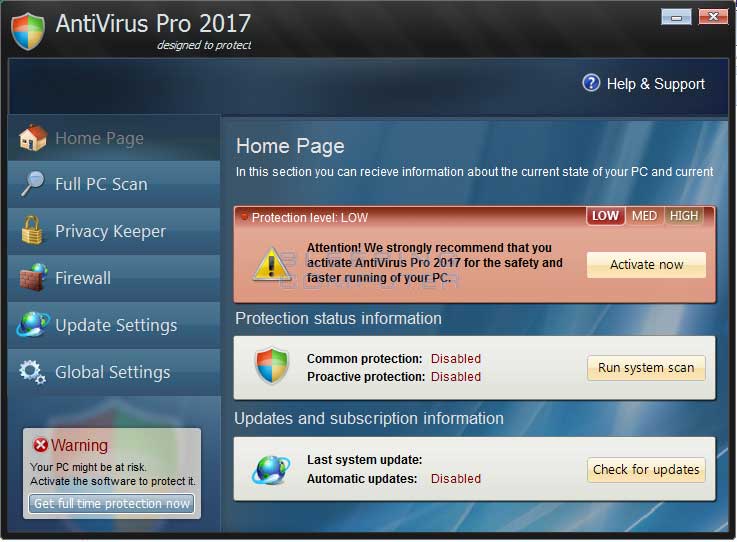
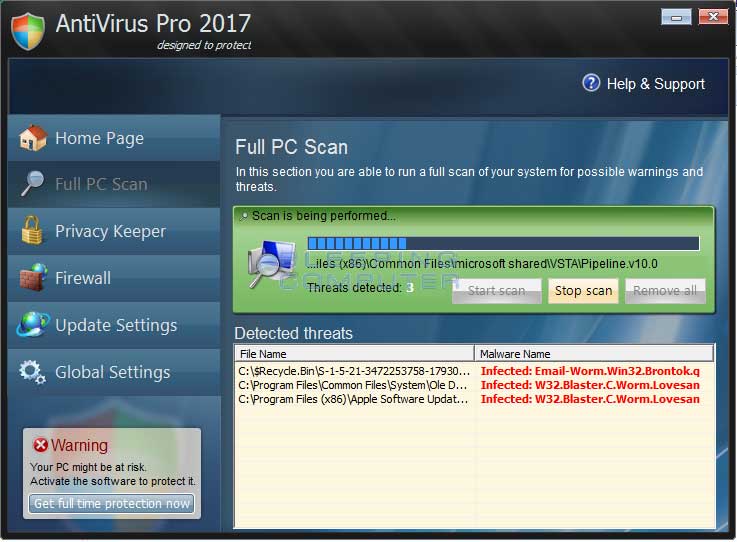
AntiVirus Pro 2017 is a computer infection from the Rogue.WinPCDefender family of rogue anti-spyware programs. This program is classified as a rogue because it deliberately displays false scan results, fake security alerts, and prevents you from running any programs on your computer. This program is promoted through fake online antimalware scanners and as a program required to view online videos. Once installed, AntiVirus Pro 2017 will automatically scan your computer and then state that there are numerous infections on your computer. If you attempt to remove any of these so-called infections it will state that you first need to purchase the program in order to remove anything. As many of the detected files are actually legitimate, please do not manually delete anything that this rogue detects as it may affect the proper operating of Windows and your installed programs. Instead ignore the scan results and proceed with the rest of the removal guide.
While running, AntiVirus Pro 2017 will also display fake security alerts that are designed to make you think your computer is severely infected. An example of two of these alerts are:
Security Warning
Malicious program has been detected. Click here to protect your computer.FIREWALL WARNING
Hidden file transfer to remote host has been detected.
AntiVirus Pro 2017 has detected a leak of your files through the Internet. We strongly recommend that you block the attack immediately.
To protect itself from being removed, AntiVirus Pro 2017 will also not allow you to run most programs on your computer. Instead when you attempt to launch a program, AntiVirus Pro 2017 will display a message that states that the program is infected. The text of this message is:
iexplore.exe can not start
File iexplore.exe is infected by W32/Blaster.worm. Please activate AntiVirus Pro 2017 to protect your computer.
Just like the fake scan results, these fake alerts are just another tactic to scare you into purchasing the program and should be ignored.
As you can see, this program was created for the sole purpose of scaring you into thinking your computer is severely infected so that you will then purchase it. Therefore, do not purchase AntiVirus Pro 2017 for any reason, and if you already have, please contact your credit card company and state that the program is a computer infection and a scam and that you would like to dispute the charge. To remove this infection and related malware, please follow the steps in the guide below.
AntiVirus Pro 2017 Removal Options
Self Help Guide
If you are uncomfortable making changes to your computer or following these steps, do not worry! Instead you can get free one-on-one help by asking in the forums.
- Print out these instructions as we may need to close every window that is
open later in the fix.
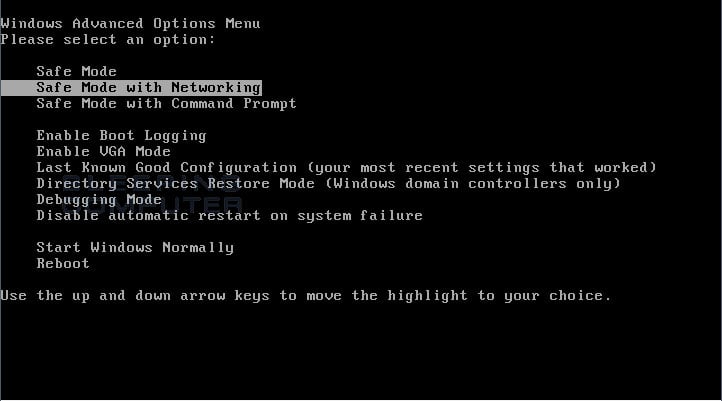
- Reboot your computer into Safe Mode with Networking. To
do this, turn your computer off and then back on and immediately when you
see anything on the screen, start tapping the F8 key on your
keyboard. Eventually you will be brought to a menu similar to the one below:

Using the arrow keys on your keyboard, select Safe Mode with Networking and press Enter on your keyboard. If you are having trouble entering safe mode, then please use the following tutorial: How to start Windows in Safe Mode
Windows will now boot into safe mode with networking and prompt you to login as a user. Please login as the same user you were previously logged in with in the normal Windows mode. Then proceed with the rest of the steps. - It is possible that the infection you are trying to remove will not allow
you to download files on the infected computer. If this is the case, then
you will need to download the files requested in this guide on another computer
and then transfer them to the infected computer. You can transfer the files
via a CD/DVD, external drive, or USB flash drive.
- Before we can do anything we must first end the processes that belong to
AntiVirus Pro 2017
so that it does not interfere with the cleaning procedure. To do this, please
download RKill to your desktop from the following link.
RKill Download Link - (Download page will open in a new tab or browser window.)
When at the download page, click on the Download Now button labeled iExplore.exe download link. When you are prompted where to save it, please save it on your desktop. - Once it is downloaded, double-click on the iExplore.exe
icon in order to automatically attempt to stop any processes associated with
AntiVirus Pro 2017
and other Rogue programs. Please be patient while the program looks for various
malware programs and ends them. When it has finished, the black window will
automatically close and you can continue with the next step. If you get a
message that RKill is an infection, do not be concerned. This message is just
a fake warning given by
AntiVirus Pro 2017
when it terminates programs that may potentially remove it. If you run into
these infections warnings that close RKill, a trick is to leave the warning
on the screen and then run RKill again. By not closing the warning, this typically
will allow you to bypass the malware trying to protect itself so that RKill
can terminate
AntiVirus Pro 2017
. So, please try running RKill until the malware is no longer running. You
will then be able to proceed with the rest of the guide. Do not reboot
your computer after running RKill as the malware programs will start again.
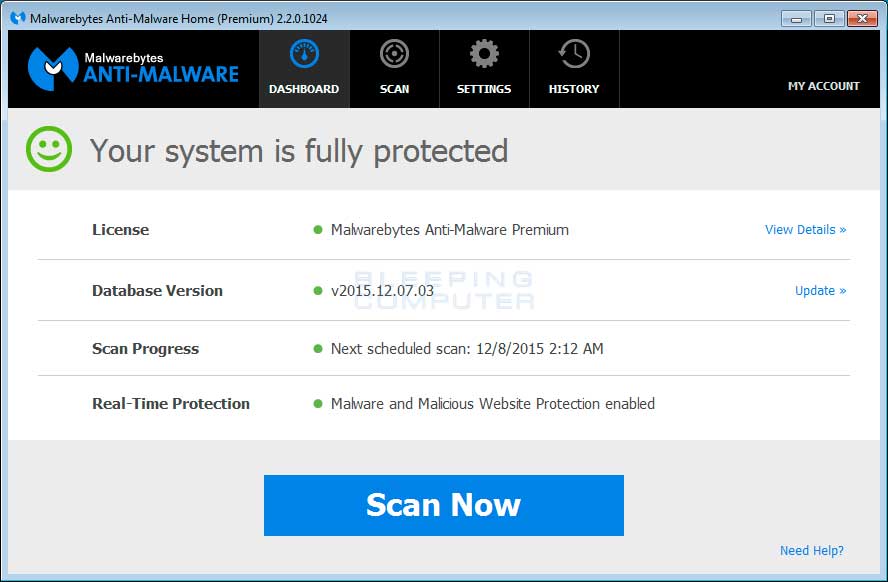
If you continue having problems running RKill, you can download the other renamed versions of RKill from the RKill download page. Both of these files are renamed copies of RKill, which you can try instead. Please note that the download page will open in a new browser window or tab. - At this point you should download Malwarebytes Anti-Malware, or MBAM, to scan your computer for any any infections or adware that may be present. Please download Malwarebytes from the following
location and save it to your desktop:
Malwarebytes Anti-Malware Download Link (Download page will open in a new window) - Once downloaded, close all programs and Windows on your computer, including
this one.
- Double-click on the icon on your desktop named mb3-setup-1878.1878-3.0.6.1469.exe.
This will start the installation of MBAM onto your computer.
- When the installation begins, keep following the prompts in order to continue
with the installation process. Do not make any changes to default settings
and when the program has finished installing, make sure you leave Launch
Malwarebytes Anti-Malware checked. Then click on the Finish button. If MalwareBytes prompts you to reboot, please do not do so.
- MBAM will now start and you will be at the main screen as shown below.

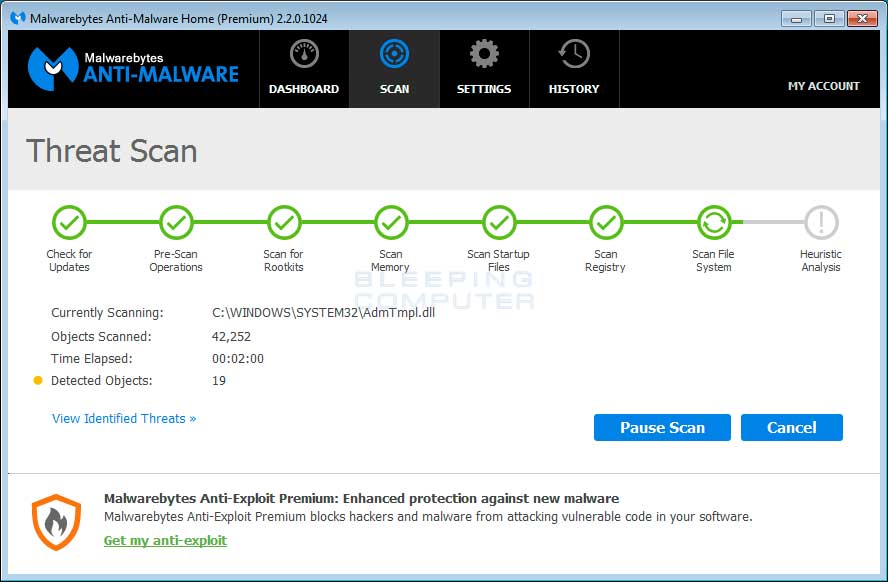
Please click on the Scan Now button to start the scan. If there is an update available for Malwarebytes it will automatically download and install it before performing the scan. - MBAM will now start scanning your computer for malware. This process can
take quite a while, so we suggest you do something else and periodically
check on the status of the scan to see when it is finished.

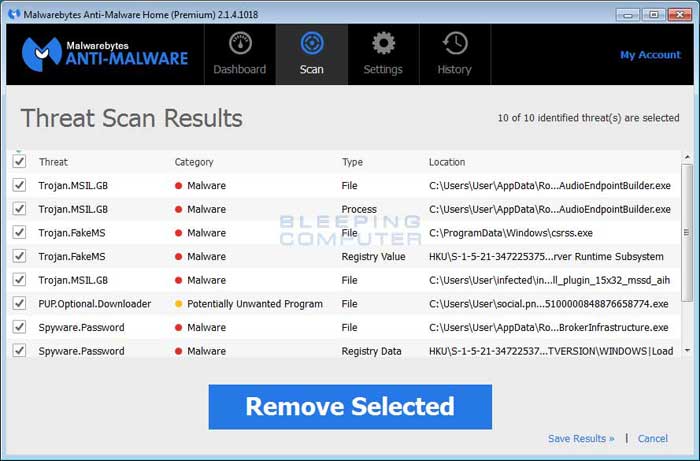
- When MBAM is finished scanning it will display a screen that displays any malware that it has detected. Please note that the infections found may be different
than what is shown in the image below due to the guide being updated for newer versions of MBAM.

You should now click on the Remove Selected button to remove all the seleted malware. MBAM will now delete all of the files and registry keys and add them to the programs quarantine. When removing the files, MBAM may require a reboot in order to remove some of them. If it displays a message stating that it needs to reboot, please allow it to do so. Once your computer has rebooted, and you are logged in, please continue with the rest of the steps. - You can now exit the MBAM program. If Malwarebytes did not prompt you to reboot your computer, please do so that you are back in normal mode.
- As many rogues and other malware are installed through vulnerabilities found
in out-dated and insecure programs, it is strongly suggested that you use
Secunia PSI to scan for vulnerable programs on your computer. A tutorial on
how to use Secunia PSI to scan for vulnerable programs can be found here:
How to detect vulnerable and out-dated programs using Secunia Personal Software Inspector
Your computer should now be free of the AntiVirus Pro 2017 program. If your current anti-virus solution let this infection through, you may want to consider purchasing the PRO version of Malwarebytes Anti-Malware to protect against these types of threats in the future.