Table of Contents
- How to get help with CryptoDefense
- What is CryptoDefense or the HOW_DECRYPT.txt Ransomware
- How to decrypt files encrypted by CryptoDefense
- How to restore files encrypted by CryptoDefense using the Emsisoft Decryptor
- How to restore files encrypted by CryptoDefense using Shadow Volume Copies
- Information about the Malware Developer's CryptoDefense Decrypt Service Site
- Known Bitcoin Payment addresses for CryptoDefense
- How to prevent your computer from becoming infected by CryptoDefense
- How to allow specific applications to run when using Software Restriction Policies
How to get help with CryptoDefense
If you are infected the with CryptoDefense, or HOW_DECRYPT.txt, ransomware you can use this guide to learn more about the infection and what you can do once you are infected. At this time, there is method to decrypt your files that works 50% of the time. For instructions on how to decrypt your files, please see this section. I would like to thank Fabian Wosar, DecrypterFixer and Steven Wooton for there assistance with gathering information on this infection.
There is an active CryptoDefense support topic, which contains discussion and the experiences of a variety of IT consultants, end users, and companies who have been affected by CryptoDefense. This topic also contains information on how to attempt restoring files that were encrypted by CryptoDefense. If you are interested in this infection or wish to ask questions about it, please visit this CryptoDefense support topic. Once at the topic, and if you are a member, you can subscribe to it in order to get notifications when someone adds more information to the topic.
What is CryptoDefense or the How_Decrypt Ransomware
CryptoDefense is a ransomware program that was released around the end of February 2014 that targets all versions of Windows including Windows XP, Windows Vista, Windows 7, and Windows 8. When a computer is infected, the infection will perform the following actions:
- Connects to the Command and Control server and uploads your private key.
- Deletes all Shadow Volume Copies so that you cannot restore your files form the Shadow Volumes. This means you will only be able to restore your files by restoring from backup or paying the ransom. In some cases the infection does not properly clear the shadow copies, so you may want to use the instructions below to see if you can restore from them.
- Scan your computer and encrypt data files such as text files, image files, video files, and office documents.
- Create a screenshot of your active Windows screen and upload it their Command & Control server. This screen shot will be inserted in your payment page on their Decrypt Service site, which is explained further in this FAQ.
- Creates a How_Decrypt.txt and How_Decrypt.html file in every folder that a file was encrypted. The HTML and TXT files will contain instructions on how to access a payment site that can be used to send in the ransom.
- Creates a HKCU\Software\<unique ID>\ registry key and stores various configuration information in it. It will also list all the encrypted files under the HKCU\Software\<unique ID>\PROTECTED key.
This payment site is located on the Tor network and you can only make the payment in Bitcoins. Though this infection has numerous similarities to CryptoLocker or CryptorBit, there is no evidence that they are related. In order to purchase the decryptor for your files you need to pay a $500 USD ransom in Bitcoins. If you do not pay the ransom within 4 days it will double to $1,000 USD. They also state that if you do not purchase a decryptor within one month, they will delete your private key and you will no longer be able to decrypt your files.
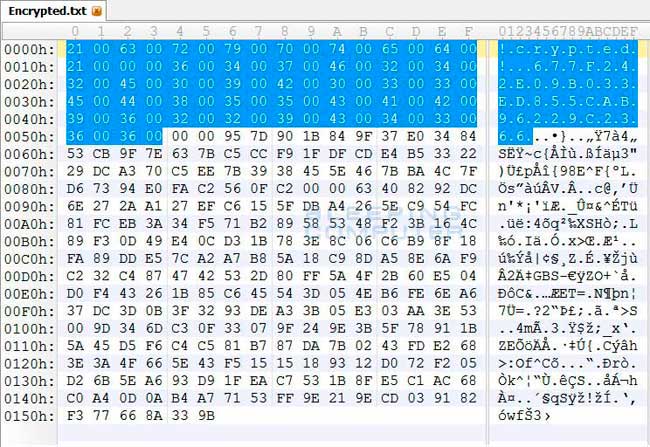
The files are encrypted using RSA-2048 encryption, which makes them impossible to decrypt via brute force methods. At the beginning of each encrypted file will be two strings of text. The first string is !crypted! and the second string is a unique identifier for the infected computer. An example identifier is 18177F25DA00CD4CBC3D1b8B9F55F018. All encrypted files on the same computer will contain the same unique identifier. This identifier is probably used by the Decrypt Service web site to identify the private key that can be used to decrypt the file when performing a test decryption. You can see these strings of text in a hex editor as shown below:
Based on research performed by DecrypterFixer, it appears that this infection is installed through programs that pretend to be flash updates or video players required to view an online video. When these downloads are run, numerous adware will be installed along with CryptoDefense. From screenshots of other infected computers, it is also not uncommon for infected computer's to also have CryptoLocker or CryptorBit installed on them as well.
How to decrypt files encrypted by CryptoDefense
If you were infected by CryptoDefense on April 1st 2014 or before, then there is a chance you can recover the decryption key that can be used to decrypt your files. This is because the malware developer had a flaw in the CryptoDefense program that left behind the public decryption key. Fabian Wosar of Emsisoft discovered this flaw and had created a decrypter that could potentially retrieve the key and decrypt your files. Fabian, and others, were then helping victims privately on how to use this tool so that the malware developer would not know how to fix the flaw in their program. Unfortunately, Symantec decided to blog about this flaw, instead of keeping it quiet, which led the malware developer to update CryptoDefense so it no longer leaves behind the key. In my opinion, this was irresponsible as Symantec chose publicity over helping the victims.
With this said, if you were infected with CryptoDefense before April 1st 2014, you should read the following section in order to attempt to retrieve your key and decrypt your files:
How to restore files encrypted by CryptoDefense using the Emsisoft Decryptor
If the Emsisoft's tool is unable to retrieve your decryption key, then your only other method is to try and restore your from a shadow copy. As CryptoDefense attempts to clear your shadow copies when it is installed this may not work either. Please note that Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, & Windows 8.
How to restore files encrypted by CryptoDefense using Shadow Volume Copies
Unfortunately, if none of the above methods work, your only alternative will be to restore from an available backup.
How to restore files encrypted by CryptoDefense using the Emsisoft Decryptor
If you were infected before April 1st, 2014 then you may have been infected with a variant that mistakenly left the private decryption key behind on the computer. To begin please download decrypt_cryptodefense.zip from the following URL and save it to your desktop.
Once the file has been downloaded, right-click on the file and select Extract All ... . An extraction wizard will open that will guide you through the encryption process. If you left all of the check marks checked during the extraction wizard, the extracted folder will automatically open.
Inside the folder you will see two files. One file is a tool called CryptoOffence (CryptoOffense.exe) that can be used to extract the decryption key to a file called secret.key. You only need to use this file if you wish to decrypt encrypted files using a different computer. For more information on how to use this tool, please see the How to export your key and decrypt from another computer section below.
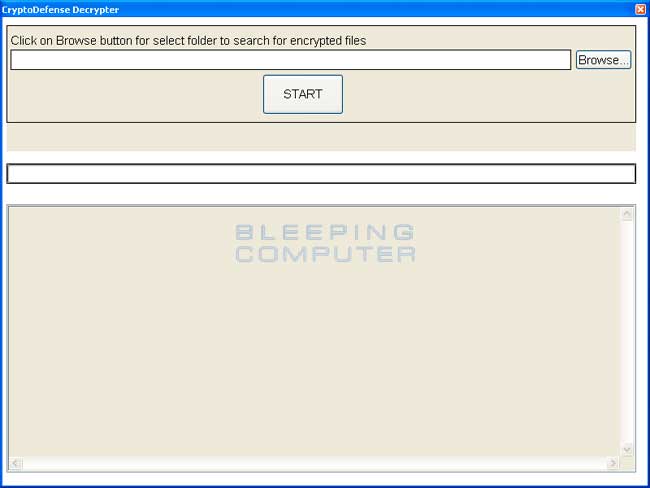
The directory also contains a tool called decrypt_cryptodefense.exe. This program is a CryptoDefense decrypter that we will be using to automatically extract the encryption key from your computer and decrypt your files. If you are logged into the infected machine as the infected user, please double-click on the decrypt_cryptodefense.exe file to launch the Emsisoft CryptoDefense Decrypter tool. When you run this file, if it is detected by your anti-virus software, please be rest-assured that the file is harmless. You can either white list the file in your anti-virus software or disable your anti-virus system for the time of decryption. For further instructions on how to do that, please refer to the manual of your anti-virus software.
The Emsisoft CryptoDefense Decrypter will now be launched and you will be shown a screen similar to the one below.
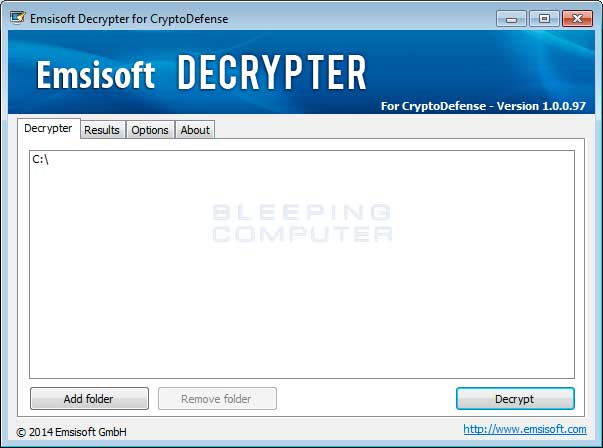
This program will recursively scan all folders that are added for encrypted files. When you are ready to start the decryption process simply click on the Decrypt button.
Emsisoft will now attempt to extract the decryption key from the logged in account. If a key is detected, you will see the following message in the log:
If a key is detected it will automatically begin to decrypt the encrypted files on your computer. This process can take quite a while, so please be patient while it processes your files. While the program decrypts your files it may appear to hang on a particular file and the program will appear to not respond. This is normal and when it has finished decrypting the file it will start responding again.
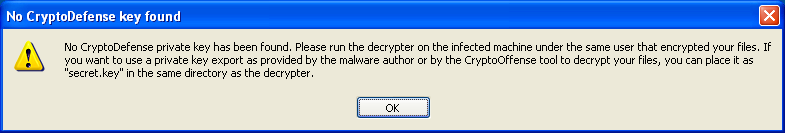
When you run decrypt_cryptodefense.exe, it if is unable to extract the key it will display the alert shown below and unfortunately not be able to decrypt your files.
If the program was able to recover and load the key, but you are receiving errors that state File could not be decrypter properly. Skipping ... then your key may have been overwritten. Examples of this happening can be seen in the image below.
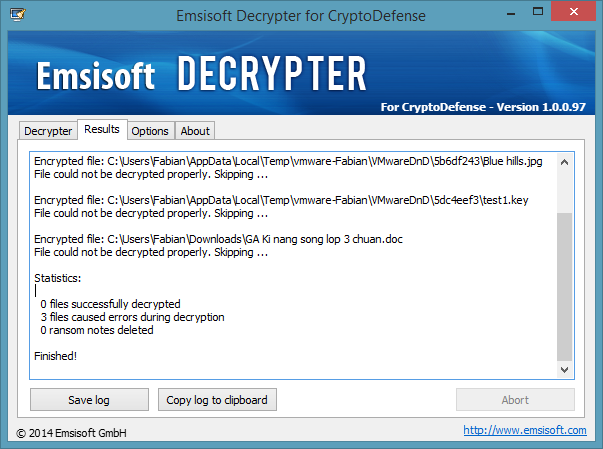
In this situation we have one last chance of possibly recovering your decryption key. The decryption key is stored in the %appdata%\Microsoft\Crypto\RSA folder. If your Shadow Volume Copies are intact you can restore that folder to a previous version in the hopes that you will be restoring the key that encrypted your files. You can then run the decrypt_cryptodefense.exe program again and see if it can load the correct key and decrypt your files.
Before you restore your RSA folder it is strongly suggested that you backup your %appdata%\Microsoft\Crypto\RSA folder. Also if you are using EFS, then be careful with restoring your RSA folder. At a bare minimum you must backup your certificates using the instructions in this Microsoft document.
To learn how to restore the RSA folder from the Shadow Volume Copies you can read this section:
How to restore files encrypted by CryptoDefense using Shadow Volume Copies
If you run into any problems or do not feel completely comfortable following these instructions on your own, please feel free to ask for more guidance in the CryptoDefense Support Topic.
How to export your key and decrypt from another computer
If you wish to decrypt encrypted files from another computer you will need to perform some additional steps. As decrypt_cryptodefense.exe will try to automatically retrieve the key from the infected computer, this will obviously not work if you run the program from a different computer. Instead you will first need to export the decryption key on the infected computer as a file called secret.key and then copy it to the computer where wish to perform the decryption.
To do this, copy the CryptoOffense.exe file from the decrypt_cryptodefense.zip file to the infected computer. When logged in as the infected user, run the CryptoOffense.exe program. If everything works, you will see output like this:
You will now find a new file named "secret.key" in the same directory as the CryptoOffense.exe program you just ran. You can then copy that secret.key file to your decryption computer and place it in the same folder as the decrypt_cryptodefense.exe tool. Now when you run decrypt_cryptodefense.exe on the decryption computer it will automatically load the secret.key and allow you to decrypt the files.
How to restore files encrypted by CryptoDefense using Shadow Volume Copies
If you had System Restore enabled on the computer, Windows creates shadow copy snapshots that contain copies of your files from that point of time when the system restore snapshot was created. These snapshots may allow us to restore a previous version of our files from before they had been encrypted. This method is not fool proof, though, as even though these files may not be encrypted they also may not be the latest version of the file. Also, CryptoDefense tries to clear these shadow copies, so they may not contains your documents after you become infected. Please note that Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, & Windows 8.
In this section we provide two methods that you can use to restore files and folders from the Shadow Volume Copy. The first method is to use native Windows features and the second method is to use a program called ShadowExplorer. It does not hurt to try both and see which methods work better for you.
Using native Windows Previous Versions:
To restore individual files you can right-click on the file, go into Properties, and select the Previous Versions tab. This tab will list all copies of the file that have been stored in a Shadow Volume Copy and the date they were backed up as shown in the image below.
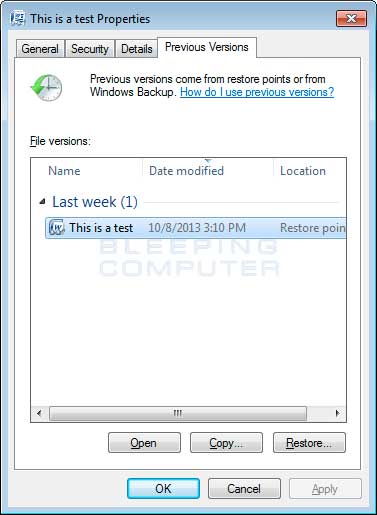
To restore a particular version of the file, simply click on the Copy button and then select the directory you wish to restore the file to. If you wish to restore the selected file and replace the existing one, click on the Restore button. If you wish to view the contents of the actual file, you can click on the Open button to see the contents of the file before you restore it.
This same method can be used to restore an entire folder. Simply right-click on the folder and select Properties and then the Previous Versions tabs. You will then be presented with a similar screen as above where you can either Copy the selected backup of the folder to a new location or Restore it over the existing folder.
Using ShadowExplorer:
You can also use a program called ShadowExplorer to restore entire folders at once. When downloading the program, you can either use the full install download or the portable version as both perform the same functionality.
When you start the program you will be shown a screen listing all the drives and the dates that a shadow copy was created. Select the drive (blue arrow) and date (red arrow) that you wish to restore from. This is shown in the image below.
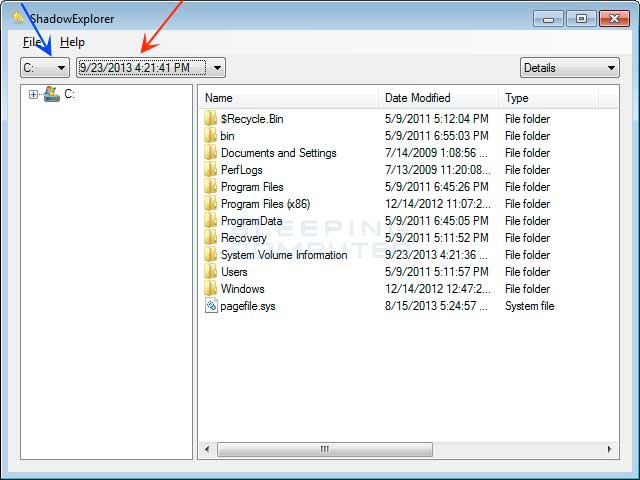
To restore a whole folder, right-click on a folder name and select Export. You will then be prompted as to where you would like to restore the contents of the folder to.
Information about the Malware Developer's CryptoDefense Decryptor Site
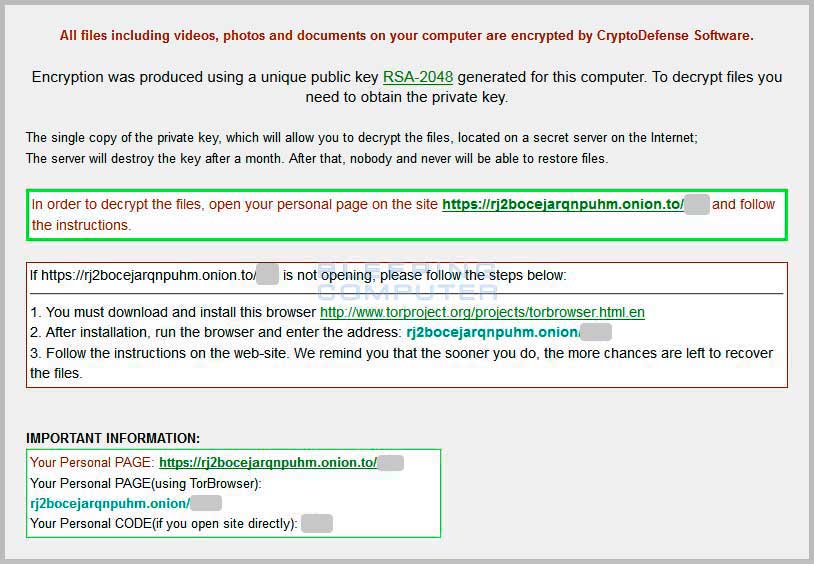
When you are infected with CryptoDefense, the infection will create How_Decrypt.txt and How_Decrypt.html files that contain information on how to pay the ransom. Below is the contents of the How_Decrypt.txt and How_Decrypt.html messages:
How_Decrypt.txt:
How_Decrypt.html
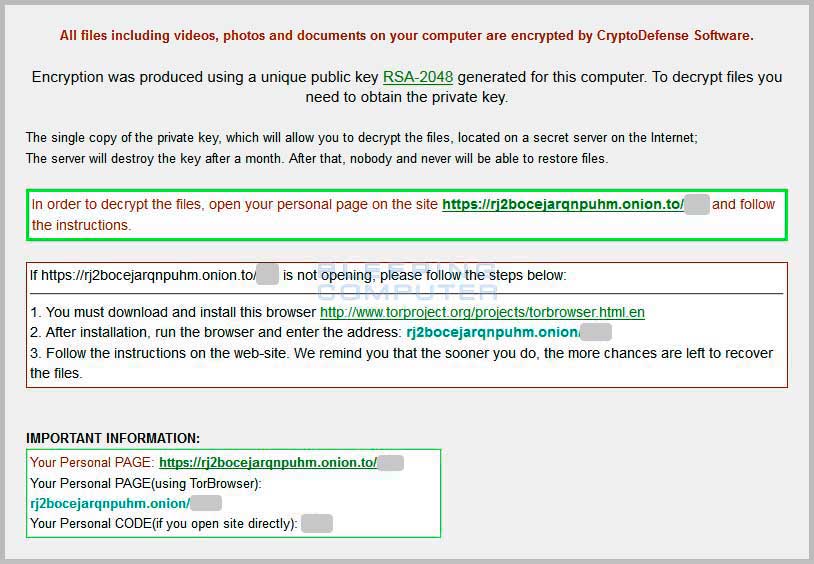
Click on the image above to see full size and other associated images.
The instructions tell the victim that in order to pay the ransom they need to go to a special Decrypt Service site where they can enter their personal code and access they payment page. This site can be accessed via the Tor address rj2bocejarqnpuhm.onion or through https://rj2bocejarqnpuhm.onion.to using a normal browser. When a user visits the Decrypt Service site they will be presented with a page that contains information about how much they need to pay to purchase the decryption program. The site will also contains a Frequently Asked Questions page, a page that shows the screen shot of your active Windows screen from when you became infected, and a page where you can perform a test decryption on one file.
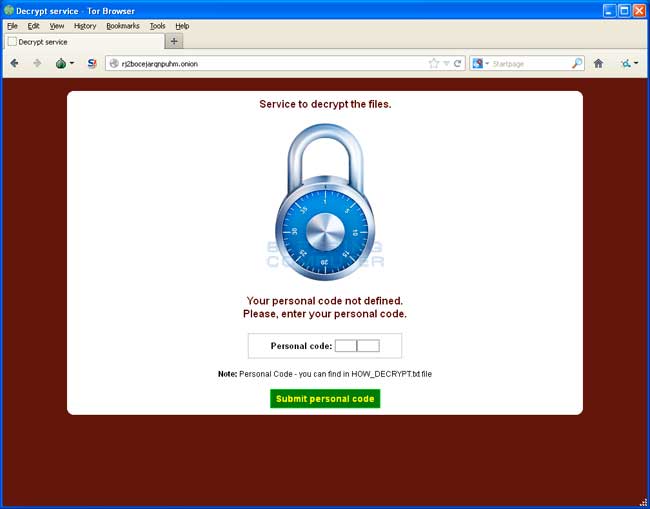
Click on the image above to see full size and other associated images.
In order to pay the ransom, you will need to send the requested bitcoins to the listed bitcoin address. Once you send the bitcoins you then need to submit the transaction ID on their site and click on the Pay button. Once the transaction has been verified you will be given a link where you can download the decryptor, which is shown below.
When you run the decryptor it will read the registry to find files that need to be decrypted. If the registry entries do not exist it will prompt you to specify a folder to scan for encrypted files.
Known Bitcoin Payment addresses for CryptoDefense
CryptoDefense allows you to pay the ransom by sending bitcoins to an address shown in the CryptoDefense Decrypt Service page. Bitcoins are currently worth over $600 USD on some bitcoins exchanges. The Bitcoin addresses used by CryptoDefense to receive payments are:
https://blockchain.info/address/19DyWHtgLgDKgEeoKjfpCJJ9WU8SQ3gr27
You can use the links above to see transactions into the wallet and out of the wallet. You can typically tell which payments to this address are from ransom victims as there will be many payments with similar amounts.
How to prevent your computer from becoming infected by CryptoDefense
You can use the Windows Group or Local Policy Editor to create Software Restriction Policies that block executables from running when they are located in specific paths. For more information on how to configure Software Restriction Policies, please see these articles from MS:
http://support.microsoft.com/kb/310791
http://technet.microsoft.com/en-us/library/cc786941(v=ws.10).aspx
The file paths that have been used by this infection and its droppers are:
C:\<random>\<random>.exe
C:\Users\<User>\AppData\Local\<random>.exe (Vista/7/8)
C:\Users\<User>\AppData\Local\<random>.exe (Vista/7/8)
C:\Documents and Settings\<User>\Application Data\<random>.exe (XP)
C:\Documents and Settings\<User>\Local Application Data\<random>.exe (XP)
%Temp%
In order to block the CryptoDefense you want to create Path Rules so that they are not allowed to execute. To create these Software Restriction Policies, you can either use the CryptoPrevent tool or add the policies manually using the Local Security Policy Editor or the Group Policy Editor. Both methods are described below.
How to use the CryptoPrevent Tool:
FoolishIT LLC was kind enough to create a free utility called CryptoPrevent that automatically adds the suggested Software Restriction Policy Path Rules listed above to your computer. This makes it very easy for anyone using Windows XP SP 2 and above to quickly add the Software Restriction Policies to your computer in order to prevent CryptoDefense and Zbot from being executed in the first place. This tool is also able to set these policies in all versions of Windows, including the Home versions.
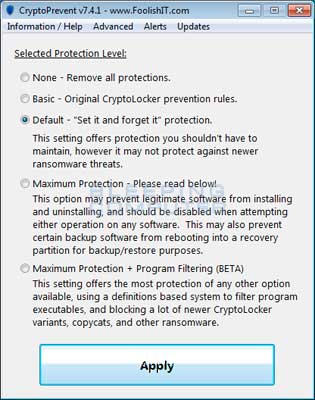
A new feature of CryptoPrevent is the option to whitelist any existing programs in %AppData% or %LocalAppData%. This is a useful feature as it will make sure the restrictions that are put in place do not affect legitimate applications that are already installed on your computer. To use this feature make sure you check the option labeled Whitelist EXEs already located in %appdata% / %localappdata% before you press the Block button.
You can download CryptoPrevent from the following page:
For more information on how to use the tool, please see this page:
Once you run the program, simply click on the Apply Protection button to add the default Software Restriction Policies to your computer. If you wish to customize the settings, then please review the checkboxes and change them as necessary. If CryptoPrevent causes issues running legitimate applications, then please see this section on how to enable specific applications. You can also remove the Software Restriction Policies that were added by clicking on the Undo button.
How to manually create Software Restriction Policies to block CryptoDefense:
In order to manually create the Software Restriction Policies you need to be using Windows Professional or Windows Server. If you want to set these policies for a particular computer you can use the Local Security Policy Editor. If you wish to set these policies for the entire domain, then you need to use the Group Policy Editor. Unfortunately, if you are a Windows Home user, the Local Policy Editor ir not available and you should use the CryptoPrevent tool instead to set these policies. To open the Local Security Policy editor, click on the Start button and type Local Security Policy and select the search result that appears. You can open the Group Policy Editor by typing Group Policy instead. In this guide we will use the Local Security Policy Editor in our examples.
Once you open the Local Security Policy Editor, you will see a screen similar to the one below.
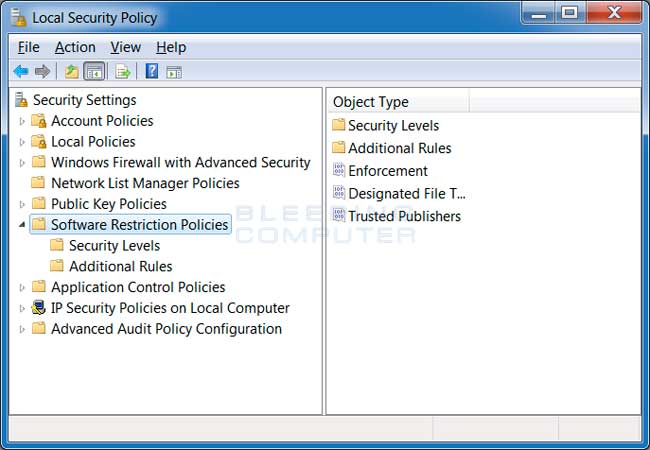
Once the above screen is open, expand Security Settings and then click on the Software Restriction Policies section. If you do not see the items in the right pane as shown above, you will need to add a new policy. To do this click on the Action button and select New Software Restriction Policies. This will then enable the policy and the right pane will appear as in the image above. You should then click on the Additional Rules category and then right-click in the right pane and select New Path Rule.... You should then add a Path Rule for each of the items listed below.
If the Software Restriction Policies cause issues when trying to run legitimate applications, you should see this section on how to enable specific applications.
Below are a few Path Rules that are suggested you use to not only block the infections from running, but also to block attachments from being executed when opened in an e-mail client.
Block CryptoDefense executable in %AppData%
Path: %AppData%\*.exe
Security Level: Disallowed
Description: Don't allow executables to run from %AppData%.Block CryptoDefense executable in %LocalAppData%
Path if using Windows XP: %UserProfile%\Local Settings\*.exe
Path if using Windows Vista/7/8: %LocalAppData%\*.exe
Security Level: Disallowed
Description: Don't allow executables to run from %AppData%.Block Zbot executable in %AppData%
Path: %AppData%\*\*.exe
Security Level: Disallowed
Description: Don't allow executables to run from immediate subfolders of %AppData%.Block Zbot executable in %LocalAppData%
Path if using Windows XP: %UserProfile%\Local Settings\*\*.exe
Path if using Windows Vista/7/8: %LocalAppData%\*\*.exe
Security Level: Disallowed
Description: Don't allow executables to run from immediate subfolders of %AppData%.Block executables run from archive attachments opened with WinRAR:
Path if using Windows XP: %UserProfile%\Local Settings\Temp\Rar*\*.exe
Path if using Windows Vista/7/8: %LocalAppData%\Temp\Rar*\*.exe
Security Level: Disallowed
Description: Block executables run from archive attachments opened with WinRAR.Block executables run from archive attachments opened with 7zip:
Path if using Windows XP: %UserProfile%\Local Settings\Temp\7z*\*.exe
Path if using Windows Vista/7/8: %LocalAppData%\Temp\7z*\*.exe
Security Level: Disallowed
Description: Block executables run from archive attachments opened with 7zip.Block executables run from archive attachments opened with WinZip:
Path if using Windows XP: %UserProfile%\Local Settings\Temp\wz*\*.exe
Path if using Windows Vista/7/8: %LocalAppData%\Temp\wz*\*.exe
Security Level: Disallowed
Description: Block executables run from archive attachments opened with WinZip.Block executables run from archive attachments opened using Windows built-in Zip support:
Path if using Windows XP: %UserProfile%\Local Settings\Temp\*.zip\*.exe
Path if using Windows Vista/7/8: %LocalAppData%\Temp\*.zip\*.exe
Security Level: Disallowed
Description: Block executables run from archive attachments opened using Windows built-in Zip support.
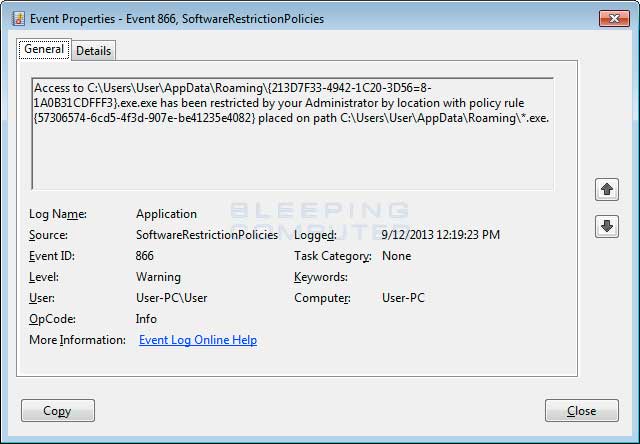
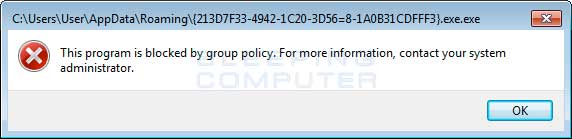
You can see an event log entry and alert showing an executable being blocked:
If you need help configuring this, feel free to ask in the CryptoDefense help topic.
How to allow specific applications to run when using Software Restriction Policies
If you use Software Restriction Policies, or CryptoPrevent, to block CryptoDefense you may find that some legitimate applications no longer run. This is because some companies mistakenly install their applications under a user's profile rather than in the Program Files folder where they belong. Due to this, the Software Restriction Policies will prevent those applications from running.
Thankfully, when Microsoft designed Software Restriction Policies they made it so a Path Rule that specifies a program is allowed to run overrides any path rules that may block it. Therefore, if a Software Restriction Policy is blocking a legitimate program, you will need to use the manual steps given above to add a Path Rule that allows the program to run. To do this you will need to create a Path Rule for a particular program's executable and set the Security Level to Unrestricted instead of Disallowed as shown in the image below.

Once you add these Unrestricted Path Rules, the specified applications will be allowed to run again.